A Security Operations Center (SOC) team is tasked with continuously monitoring its environment to detect, analyze, and respond to remarkable cybersecurity events that might become incidents, ultimately improving the security posture of the organization.
However, for SOC teams to effectively monitor their environment, it is not enough to simply deploy security systems and tools that alert them to an indiscriminate number of events. They need to know what internal or external threat actors are doing, what their activity may look like, and how to find traces of said activity across their infrastructure.
Usually, the traces left behind by threat actors and picked up by the monitoring systems or hunting teams will be known as observables or indicators of compromise (IOCs)—IP addresses, host and domain names, email addresses, filenames, file hashes, and even log entries such as unusual login attempts —which, on their own and out of context, won’t be enough to conduct an in-depth investigation.
For a proper analysis that can lead to an effective assessment, including correlation to known or trending attacks as well as potential attribution, SOC analysts need to enrich and contextualize the traces found in their internal systems. This is where internal information and especially threat intelligence can help.
Threat Intelligence: Sources, Feeds, Platforms, and Providers 🔗︎
Threat intelligence is actionable and timely knowledge rooted in data. It provides analysts with the necessary context to understand threat actors’ motivations, methods, tools, and infrastructure, helping them prevent or mitigate attacks.
Practically speaking, threat intelligence relevant to an organization is generated by combining the traces found in the organization’s internal telemetry—such as firewall and event logs—with industry-specific threat data and information obtained through different intel sources, feeds, platforms, or providers.
Sources and Feeds 🔗︎
Two common threat intelligence sources are open-source intelligence (OSINT) and threat intelligence feeds. OSINT refers to intelligence derived from publicly available information, which is collected, analyzed, and shared to support specific investigations. Threat intelligence feeds are non-prioritized streams of data or digital artifacts and focus on specific areas or data types, such as suspicious domains, malicious URLs, known malware hashes, and IP addresses associated with malicious activity, among others.
While free threat intelligence feeds are usually gathered from open sources, paid threat intelligence feeds provide curated and contextualized data from closed sources, such as the dark web and cybercrime forums, or they may aggregate and process open-source feeds.
Platforms and Providers 🔗︎
A threat intelligence platform (TIP) is software used to organize several feeds—both free and paid—into a single stream. It makes them actionable across different protection, detection, and reaction tools.
Lastly, a threat intelligence provider is a vendor that collects and produces threat intelligence indicators and reports, sometimes using a mix of human and automated analysis. The provider then offers the intelligence via premium data feeds, as a report (an example would be the Mandiant’s APT1 report), or as part of a software product.
The human-generated part may include motivations, tactics, techniques, and procedures (TTPs) and attribution to a known actor, linking to past or ongoing campaigns, signatures for detection and hunting (such as Sigma or YARA rules), as well as response and forensic strategies. The automated part provides lists of observables in machine-readable format.
Incorporating Threat Intelligence into the SOC Team 🔗︎
It’s easy to see how one may stumble around in search of the right product to incorporate into their SOC team just by looking at the variety of options out there. With that in mind, SOC teams should first gain an insider view and comprehensive understanding of the following:
However, even with the previous elements established, it is often difficult for SOC teams to choose the threat intelligence solution best suited to them and to determine how to properly take advantage of the data it provides without further burdening the analysts.
Maltego’s Top 36 Threat Intelligence Providers for SOC Teams 🔗︎
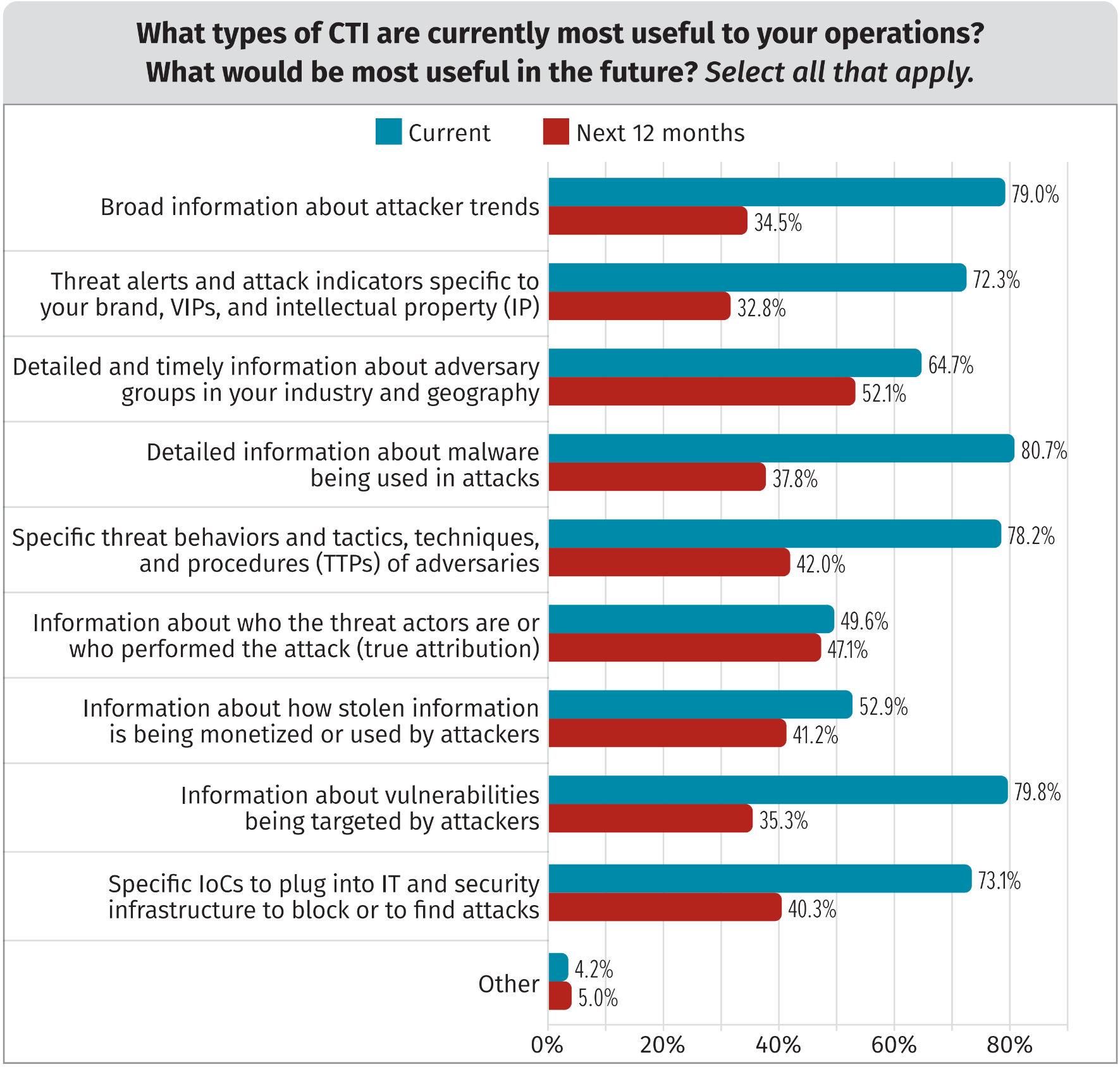
According to the 2022 SANS Cyber Threat Intelligence (CTI) Survey published in February 2022, the types of threat intelligence that are most useful for CTI operations include:
- Detailed information about malware being used in attacks
- Information about vulnerabilities being targeted by attackers
- Broad information about attacker trends
- Specific threat behaviors and TTPs of the adversary
- Specific IOCs to plug into IT and security infrastructure to block or find attacks
Source: SANS 2022 Cyber Threat Intelligence Survey
Based on these criteria, we have created a list of high-quality threat intelligence options for SOC teams that have proven to be among our end-users’ favorites and are suitable for all budget sizes.
The providers are divided into four categories:
- Infrastructure & Network Information (featured providers include: Shodan, Host.io, and VirusTotal)
- Malware, TTPs & Vulnerabilities (featured providers include: Recorded Future, Intel471, and alphaMountain)
- Deep & Dark Web / Cryptocurrency (featured providers include: CipherTrace, Silobreaker, and SpyCloud)
- Endpoint & Security Events (featured providers include: CrowdStrike, IBM QRadar, and Splunk)
The list is sorted in alphabetical order and does not indicate any ranking or preference.
Download Your Free Copy 🔗︎
Download this whitepaper for detailed descriptions and evaluations of the top threat intelligence providers. This will help you make accurate and suitable purchasing decisions for the needs and responsibilities of your SOC teams.
Don’t forget to follow us on Twitter, LinkedIn, and Mastodon, or sign up to our email newsletter for more whitepapers, case studies, and SOC tips similar to this!