When a threat actor successfully accomplishes their malicious attempt, chances are they will repeat the process and apply the same methods the next time an opportunity arises to target an unsuspecting organization.
While this may seem daunting, it can also prove to be a double-edged weapon and give us insights into established patterns, opening the door to better analysis of their behaviors.
In this article, we will guide you through methodologies for comprehending attackers’ behaviors and equip you with practical knowledge that your team can incorporate into everyday cybersecurity practices.
Table of Contents 🔗︎
Follow Trails of Threat Actors with TTPs 🔗︎
In threat analysis, we need to look at attack patterns or the methods attackers use to achieve their goals. This knowledge will help us recognize and defend against known types of attacks.
We also want to understand the specific steps involved at each stage of an attack. This requires understanding of how attackers operate, in other words, spotting their tactics, techniques, and procedures (TTPs).
What You Should Know about TTPs 🔗︎
TTPs provide us with a practical perspective, allowing us to connect operational data within the same campaign or dots in the tricky and vast cyber puzzle.
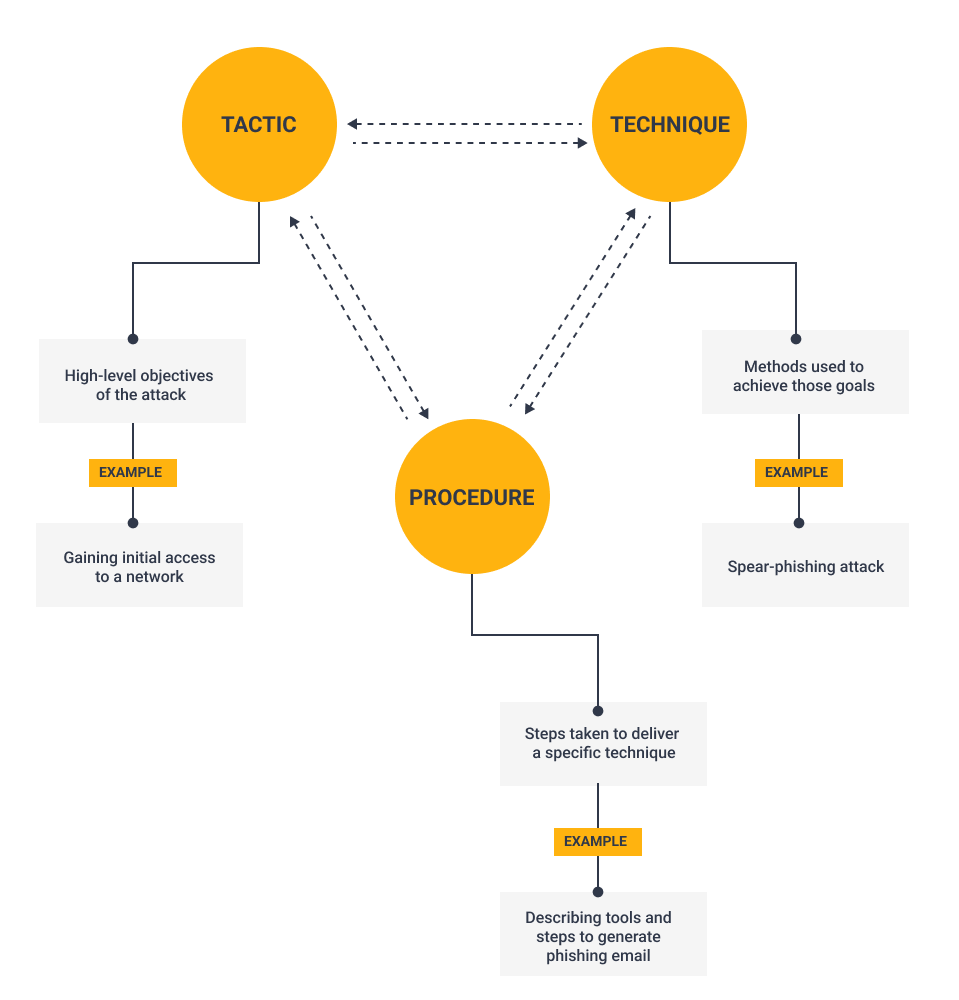
The term was borrowed from military and adopted by the cybersecurity industry to describe:
Tactics – High-level objectives of the attack Techniques – Methods used to achieve those goals Procedures – Steps taken to deliver a specific technique
If we have a broad enough view and connect the dots correctly, we can attribute TTPs to the same threat actor, understand the threat they pose, and finally, secure our organizational defenses.
TTP analysis is fundamental for proactive and reactive cybersecurity because it provides an understanding of the mindset and capabilities of your adversaries. The TTPs of our attackers do not change often and therefore can be analyzed.
What Methodologies You Can Apply in Your TTP Analysis 🔗︎
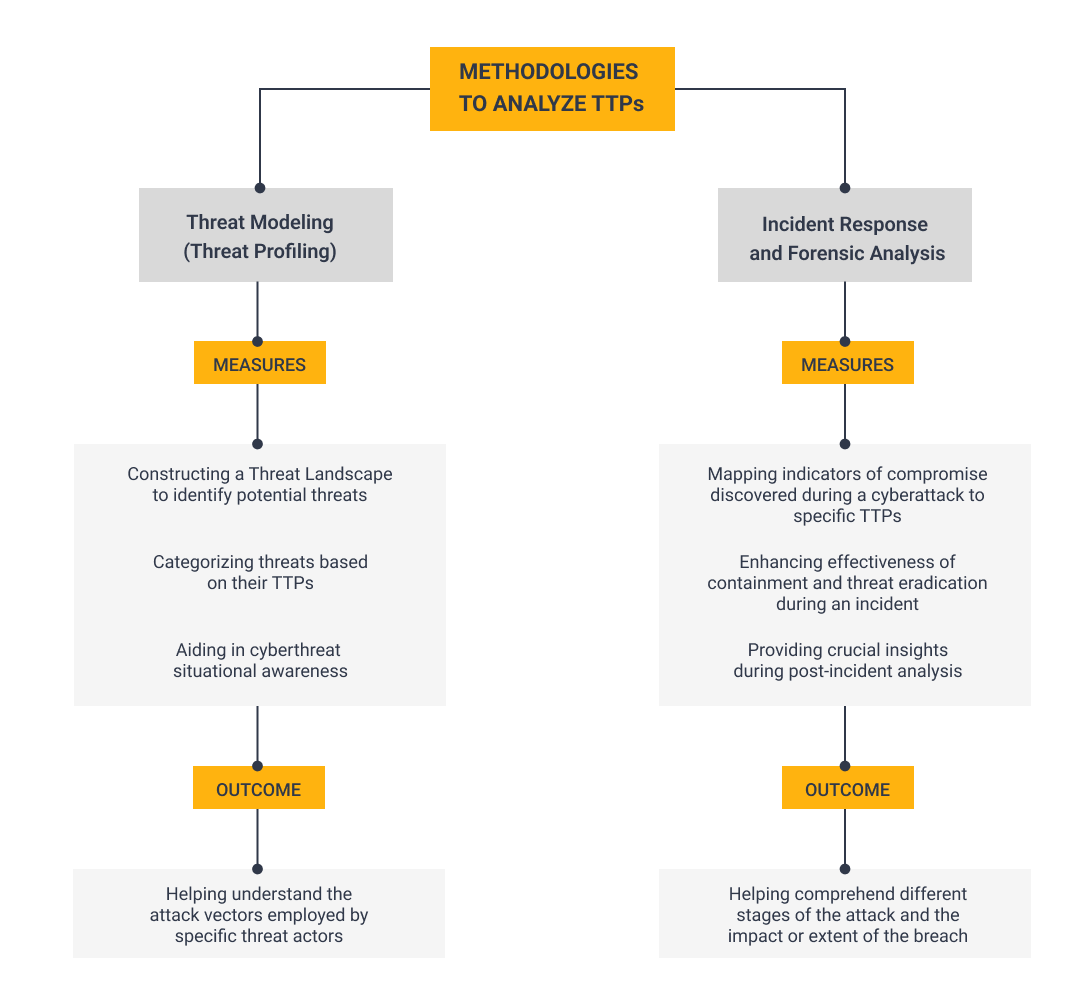
One of the most used methodologies is threat modeling, also known as threat profiling. It involves constructing a threat landscape that identifies potential threats that might be relevant to our organization and then dissecting and categorizing them based on their TTPs.
This greatly aids in cyber threat situational awareness and the understanding of the attack vectors that threat actors might employ.
On the other hand, we have other methodologies closely related to incident response and forensic analysis disciplines. These methodologies take the different indicators of compromise (IOCs) discovered during a cyberattack and map them to specific TTPs.
When employing these methodologies, analysts combine snippets of data from many disparate data sources including network data, endpoints, and centralized events, collected in platforms such as Splunk, to investigate and analyze them.
This enhances the effectiveness of containment and eradication of threats during an incident and provides crucial insights during post-incident analysis to comprehend the different stages of the attack and the impact or extent of the breach.
How TTP Analysis Can Benefit Your Team 🔗︎
Based on what we have covered, there is clear value in analyzing the TTPs of a threat actor for at least four reasons:
Technical or operational data, such as IOCs (domains, hashes, and others), are merely fingerprints that can easily change from one cyberattack or campaign to another, thus being timely.
On the other hand, TTPs provide tactical information that shapes the threat actor’s behavior which does not change frequently. By understanding the behavior and motivations of the attacker, we can better predict potential future actions or targets and develop a profile of the possible perpetrators behind these attacks.
Be Aware of the Common Attack Patterns and TTPs 🔗︎
Attack patterns or TTPs might vary from one organization to another. This only goes to show that the threat landscape, including the existing threat actors that evolve over time, depends also on who we are and where we operate.
While it may be challenging to compile a definitive list of the most common patterns, several techniques have been extensively used in recent years in global cyberattacks targeting organizations across various industries, irrespective of their specific sector.
These techniques include amongst others:
- Phishing: e.g., deceiving recipients into providing login credentials by clicking on malicious links
- Drive-by Downloads: e.g., exploiting vulnerabilities in the user’s web browser
- Ransomware: e.g., demanding payment in exchange for a decryption key or to avoid leaking the victim’s data
- Living-off-the-Land (LOTL): e.g., use of system binaries and tools instead of malware to avoid detection through masquerading
- Remote Code Execution (RCE): e.g., abusing existing software vulnerabilities to force the execution of malicious payloads
- Information Stealing: e.g., collecting credentials and other personally identifiable information (PII) that might be used to abuse or target other systems or platforms
- Command and Control (C&C) Frameworks: e.g., use of commercial or open-source C&C software to flexibly operate compromised systems
There are also different security vendors, cybersecurity agencies, and other relevant stakeholders who make predictions based on the collected intelligence regarding trends within their customer base or service constituency. These predictions are then released in annual reports that provide current information about these trends. For example, top resources include:
- CrowdStrike Global Threat Report
- Red Canary Threat Detection Report
- Verizon Data Breach Report
- SANS Institute: Five Most Dangerous New Attack Techniques
While predicting future events is difficult to incorporate into cybersecurity workflows, identifying unseen gaps or potential next steps can be facilitated by using what you may already have at your fingerprints – historical attack data.
Use Historical Attack Data to Profile Future Attackers 🔗︎
One of the most common mistakes in cyber teams is overlooking the importance of keeping a record of the encountered cyberattacks.
There is a misguided notion that relevant agencies and intelligence providers are the only ones proficient enough and responsible for collecting and understanding the necessary intelligence data. And yet, there is no substitute for the intelligence gained from your own systems and data sources.
While individual attacks or attempts may not seem significant in isolation, studying them collectively as part of campaigns can make a difference.
Here’s where you can start:
Historical data can serve as a baseline for comparison and help you make sense of ongoing activities. So, the more information you have, the better you will understand the attacker’s motivations and potential targets.
That being said, let us see what measures we can take to streamline our analysis.
Build a Toolkit for Your TTP Analysis 🔗︎
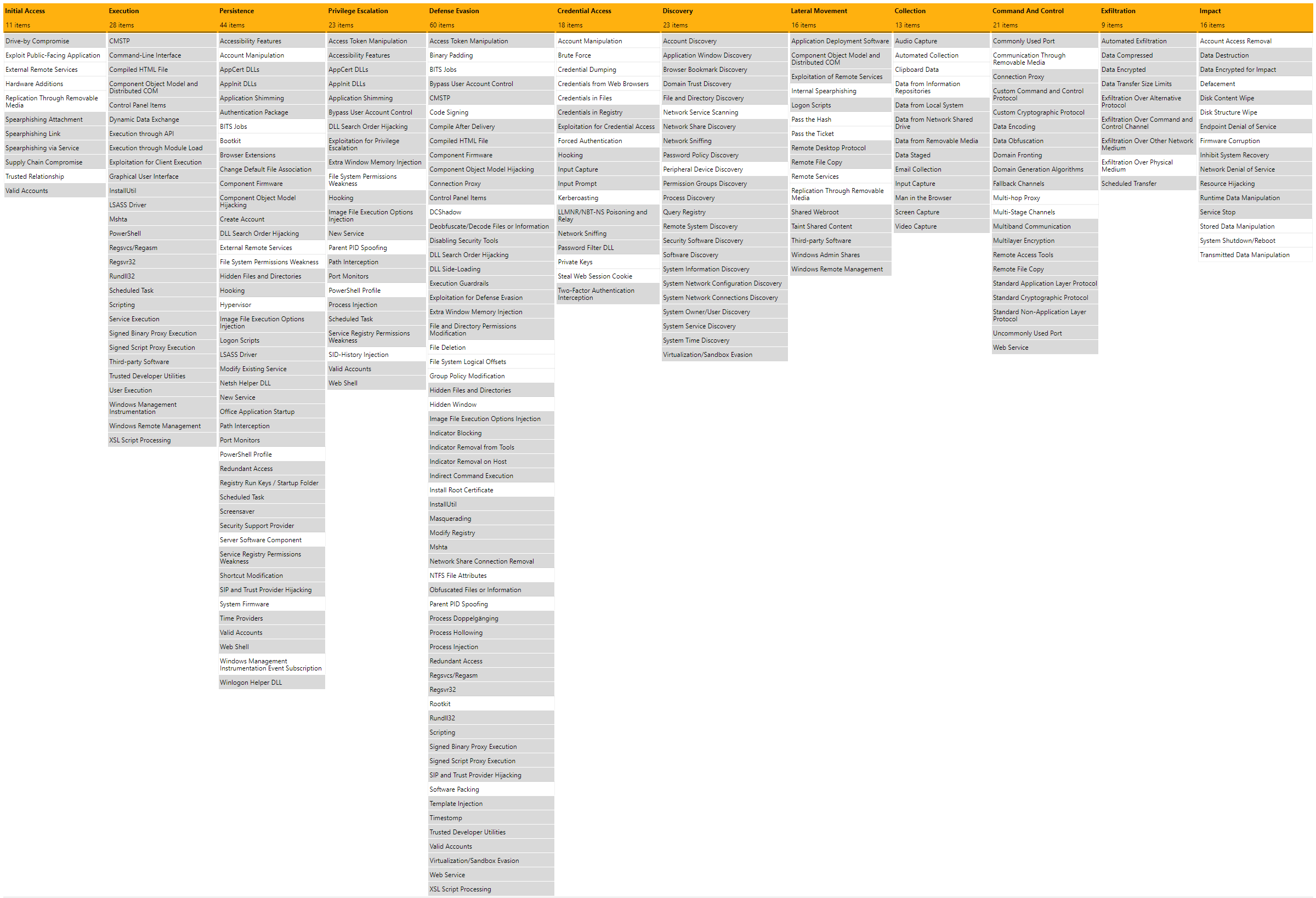
Today, we cannot discuss TTPs without mentioning the MITRE ATT&CK Framework. It serves as the industry standard and offers a knowledge base comprising common adversary tactics and techniques based on real-world observations of cyberattacks worldwide.
Both proactive and reactive cybersecurity tools have aligned their detections and references with this standard, facilitating the understanding and use of cyberattack information. One invaluable tool is the ATT&CK Navigator, which aids in annotating and exploring the framework matrices.
When analyzing TTPs, you may also want to improve the process of consolidating various pieces of information with STIX. It is the most relevant industry standard being used as a universal language that assists in the definition and exchange of Cyber Threat Intelligence (CTI) information among team members, making your workflow more interoperable and efficient.
When it comes to blue teams, they often want to assess if they have good visibility or coverage of the TTPs used by threat actors. To score and compare data log source quality, they can use handy tools such as DeTTECT. Alternatively, some teams may opt for tools like Decider. It offers guidance questions to help analysts map adversary behaviors to the framework.
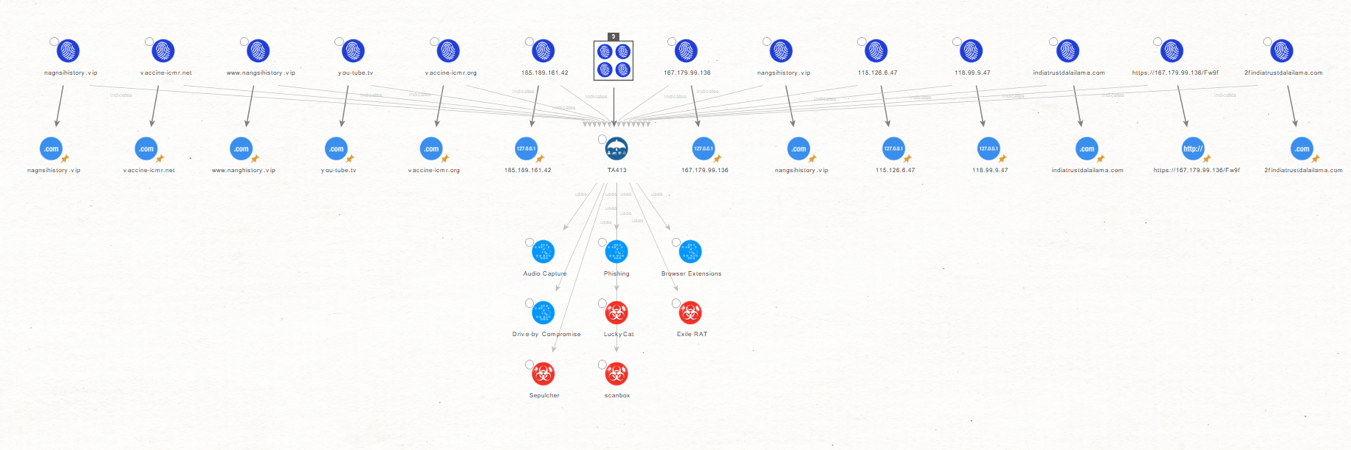
There is also a growing landscape of cyber threat intelligence tools, both open-source and made by vendors, that can effectively assist in visualizing, mapping, correlating, and dissecting TTPs to better understand and respond to cybersecurity threats.
There are different tools you can use to work with threat intelligence data. One of the most common and extended tools are Threat Intelligence Platforms (TIPs). If you want to get your hands dirty with them, you should have a try with MISP or OpenCTI. Both will provide you with a way to collect, manage, and disseminate intelligence across your organization and with other stakeholders.
Learn about Other Methods to Track Digital Traces of Your Adversary 🔗︎
In summary, analyzing TTPs gives you a deeper understanding of attackers’ moves and can help you spot anomalies and even forecast future attacks, leading to more effective daily operations.
At the same time, the sheer volume of information can feel overwhelming, and factors like limited time and resources can hinder the flow even if you are equipped with reliable methodologies and automation tools.
One idea to address these challenges is to use an all-in-one platform for data mapping and visualization to help you anticipate threats that may come your way.
For a comprehensive guide on analyzing attack patterns and TTPs and utilizing Maltego to streamline the lifecycle of threat intelligence, along with other common use cases, check out our handbook for Cyber Threat Intelligence below.
Download the resource
If you found this article useful and would like to learn more about cyber threat intelligence investigations or other related topics, you can follow us on Twitter and LinkedIn, or subscribe to our newsletter.
Happy investigating!
About the Author 🔗︎
Carlos Fragoso
Carlos is the Principal Subject Matter Expert and Lead Instructor at Maltego with over 20 years of professional experience in information security: Incident response, digital forensics, threat intelligence, and threat hunting. A curious and passionate investigator working with big companies and LEAs to tackle cybercrime around the world (Europe, Middle East, LATAM) SANS Institute Instructor.