The surface web, the deep web, and the dark web all provide useful information for analysts to explore and draw from for use in their OSINT investigations. The deep, and the dark web contain far more data compared to the surface web, and though both are used by people from all walks of life, they are often thought to be the source of a sizeable chunk of illegal activities in both the real and digital worlds.
The wealth and type of information contained in the deep and dark web, combined with the higher security access and the degree of anonymity they provide, are what have essentially turned them into prime real estate for threat actors.
By the same token, this flurry of threat actor activity has also led investigators and analysts from various industries to consider the deep and dark web as prime sources of information. However, while gaining access to data on the surface web is quite simple and performed daily, accessing data on the deep and dark web can be considerably trickier and requires more consideration and resources.
So, what are the differences between the deep and dark web? Why is the data they contain so useful not only to threat actors but to investigators and analysts alike?
In our whitepaper, you will find answers to those and more questions. It will also provide you with a list of data sources and ready-to-replicate workflows to support your deep and dark web investigations. Download now or follow along to take a look at some of the insights first!
Differences Between the Surface Web, Deep Web, and Dark Web 🔗︎
Before we delve into the deep and dark web, and why accessing data from these layers is relevant to investigations, let’s quickly touch upon the surface web.
Surface Web 🔗︎
Also known as the visible, open, or public web, the surface web is the most superficial layer of the internet and encompasses everything that is accessible via search engines that use page indexing, such as Google or Bing. Searching the surface web usually returns a good deal of results that can be narrowed down using a range of dorking techniques.
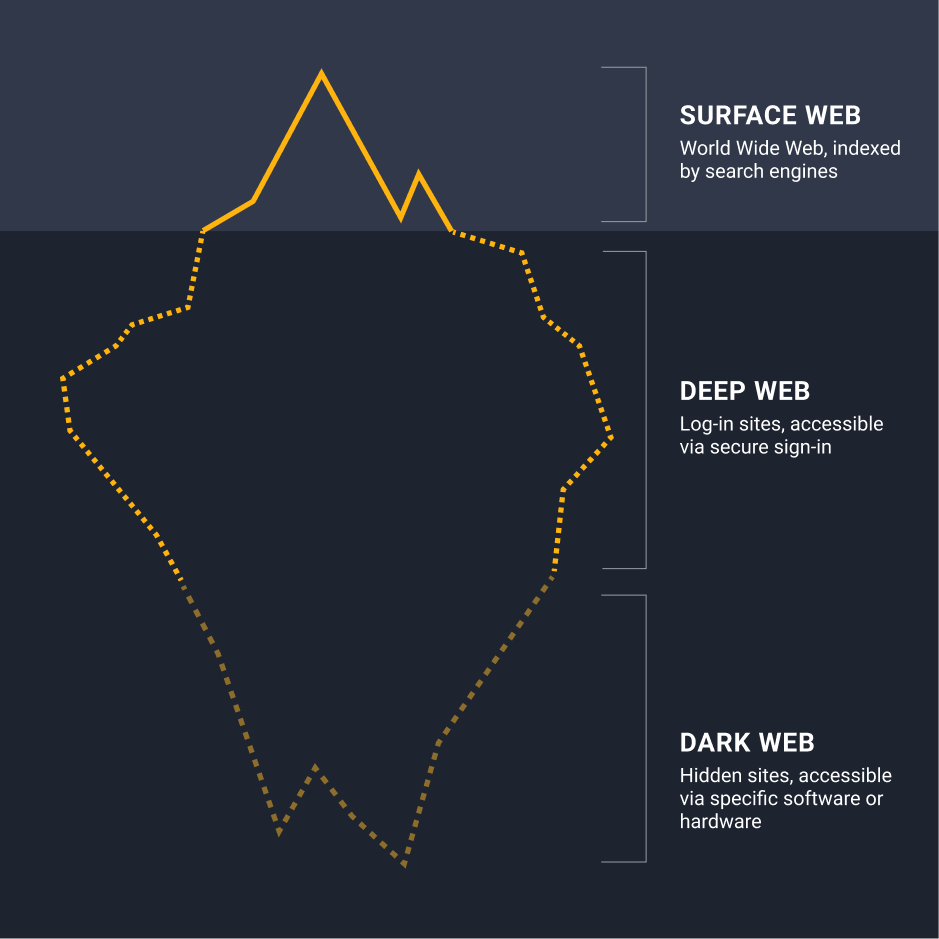
As endless as popular search engine results may often appear, surface web data still amounts to less than 5% of what is contained on the internet. It is precisely that remaining 95% that constitutes the deep and the dark web and our topic at hand.
Deep Web vs. Dark Web 🔗︎
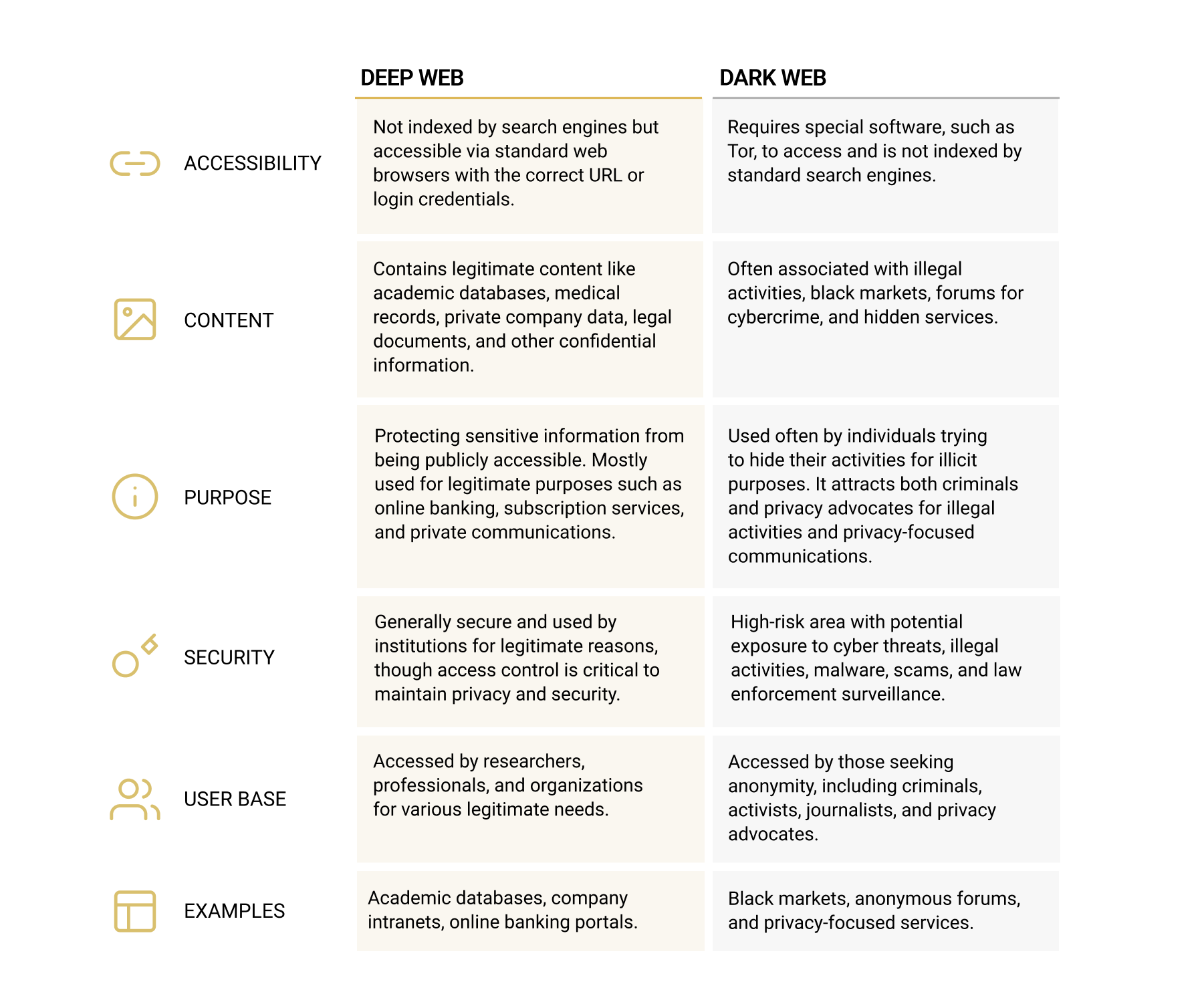
Unlike the surface web, these two layers represent the non-indexed content available on the internet. This means content which cannot be found using common search engines like Google or Bing. However, there are substantial differences between the deep and the dark web.
For instance, unlike the dark web, the deep web doesn’t require specific software to be accessed. Still, its contents can’t be identified, tracked, or crawled by standard search engines because it is either password-protected or kept behind specific internet services for privacy and security reasons.
The data contained within our email inboxes, online banking services, and even job intranets are examples of the deep web. And, as you can imagine, this data is usually only available to the user and the service providers, unless specific allowances for investigators are made in the terms of service, such as for criminal investigations.
The dark web, on the other hand, isn’t indexed by search engines and is accessible via specialized networks such as The Onion Router (TOR), I2P, or Freenet, which are designed to enable anonymous communication over the internet. This makes it a valuable source of intelligence for those who know how to navigate it.
When discussing the key differences between using conventional web browsing and accessing the dark web via specialized networks, it is necessary to distinguish between browsers like Google Chrome and entire networks like TOR.
Google Chrome utilizes standard internet protocols to access websites through easily understandable URLs. In contrast, networks such as TOR operate on unique protocols designed specifically for anonymity. These protocols then affect how URLs are structured. Unlike standard web addresses, TOR URLs are derived from the public key as part of the protocol, making them almost impossible to guess, remember, or understand.
Oftentimes, information stolen from the deep web, be it passwords or other privileged data, ends up being sold on the dark web. However, not everything that transpires there is of a criminal nature. Journalists, activists, and politicians working and reporting under corrupt or totalitarian regimes use it to gather, collaborate, and exchange information without fear of being harassed or prosecuted.
The Scope of Deep and Dark Web Investigations 🔗︎
As mentioned before, some threat actors lurk within the deep web, where they use techniques such as phishing and social engineering to steal personal data, defraud individuals, or get a foothold into a specific organization. They might then turn towards the dark web to profit from their schemes by selling the stolen data or the kits they developed for their schemes.
Others may prefer the enhanced anonymity of the deep and dark web, as it allows them to conduct their illegal activities anonymously, be it hacktivism, exchange of CSAM material, trading illegal goods, such as drugs or weapons, or disseminating content that incites violence and facilitates terrorist activities.
Because of that, analysts and investigators use data from the deep and dark web for different types of investigations:
For one, analysts can study the interactions between extremist groups, criminal organizations on dark web forums, and, in specific cases, law enforcement can use seized data from private messages to support their investigations.
For others, the deep and dark web can help bolster cybersecurity when used as a source of enrichment. This allows them to:
- confront fraud by tracking mentions of their brand and products across different forums.
- react to insider threats by tracking paste sites and chatter regarding password or data leaks.
- enhance physical security by monitoring underground chatter.
- gain insight into how their current policies and processes may be enabling criminal activities, such as human trafficking, to take place.
Where to Gather Intelligence for Deep and Dark Web Investigations 🔗︎
IMPORTANT! Before discussing where to gather this type of intelligence, it is necessary to note that investigating deep and dark web forums means that law enforcement agencies (LEAs) don’t just passively monitor these forums from a distance but actively engage in them to gather intelligence and evidence. This requires LEA officers to use undercover or sock puppet accounts to infiltrate these forums. To ensure appropriate rules are followed and protective measures are taken, each country must have legislation related to undercover agents, so it is important for investigators to operate within the established legal framework. For example, to verify if someone is selling illegal goods, LEA officers must engage in one-on-one conversations through private messages with sellers and provide proof of illegal activity. This engagement must comply with relevant laws, as not all countries permit such investigative methods.
Regarding where to gather the intelligence, there are several options to explore, starting with forums and communities where dark web users interact, monitor dark web marketplaces to observe transactions of illegal or stolen goods, and access data breach sites to enrich their findings.
Some deep web forums also have social media components or are discussed on surface web platforms, where users may share information about dark web activities. This is another valuable option for investigators, especially in the early stages of an investigation when no concrete starting point has yet been identified.
However, it is important to point out that manually searching for and collecting such intelligence is time-consuming and requires maintaining high operational security to avoid leaving digital footprints that could expose the investigator’s identity and intentions.
For these reasons, investigators may use tools like Maltego, which facilitates the process of collecting and analyzing data from the deep and dark web while keeping the searches within the tool anonymous. Using Maltego, investigators can leverage data from a number of providers of breached data and information on dark web users, their activities on forums, and more.
How can your team leverage deep and dark web intelligence in Maltego?
Download Full Version 🔗︎
Access the full version of this whitepaper now to see an extensive list of recommended sources for deep and dark web intelligence to help conduct and enrich your team’s work!
Inside, you will also find real-life examples showing how to use these sources as data integrations within Maltego, along with ready-to-replicate workflows to maximize your team’s success.
Download the resource
Don’t forget to follow us on Twitter, LinkedIn, Mastodon, and sign up to our email newsletter, so you don’t miss out on updates and news!
Happy investigating!
About the Author 🔗︎
Sergio Leal Rodriguez 🔗︎
Sergio is an experienced and dedicated professional with more than 20 years of invaluable experience in coordinating, investigating, modeling data, and researching cybercrimes with a focus on the critical field of Child Sexual Abuse at Europol’s AP TWINS. His expertise lies in coordinating multi-agency efforts as well as conducting thorough investigations, and he has actively contributed to the development of innovative methodologies for data analysis and modeling in the context of child sexual abuse.