We live in a world that is becoming more interconnected by the day. The vast amount of information shared on social media platforms offers a treasure trove of insights for the discerning eye. This is where Social Media Intelligence, also known as SOCMINT, steps in.
SOCMINT refers to the collective tools and solutions that allow cyber threat investigators to systematically organize, analyze, and interpret data from social media sources. This data, ranging from tweets, posts, images, links, and more, can be invaluable in understanding threat actors’ behaviors, patterns, and intentions.
In this article, we will delve into the world of SOCMINT and uncover its importance, applications, and challenges.
The Significance of SOCMINT for Analysis 🔗︎
For cyber threat intelligence analysts, SOCMINT is not just a supplementary source of information; it is a critical component of their investigative toolkit. The digital footprints left on social media platforms often contain a wealth of information that can reveal patterns, behaviors, and even intentions for analysts.
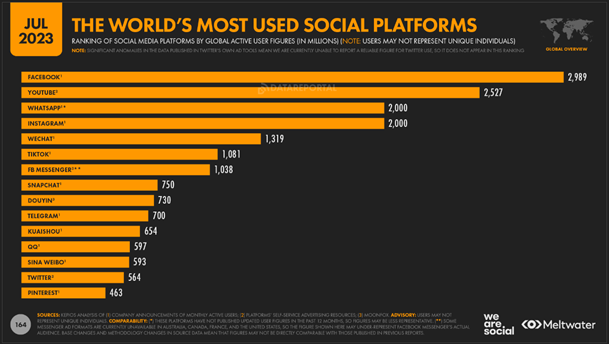
In a world where threats evolve rapidly, real-time insights from platforms with billions of interactions can be the difference between spotting a threat proactively and reacting to a breach.
The Broad Scope of SOCMINT 🔗︎
Source: datareportal
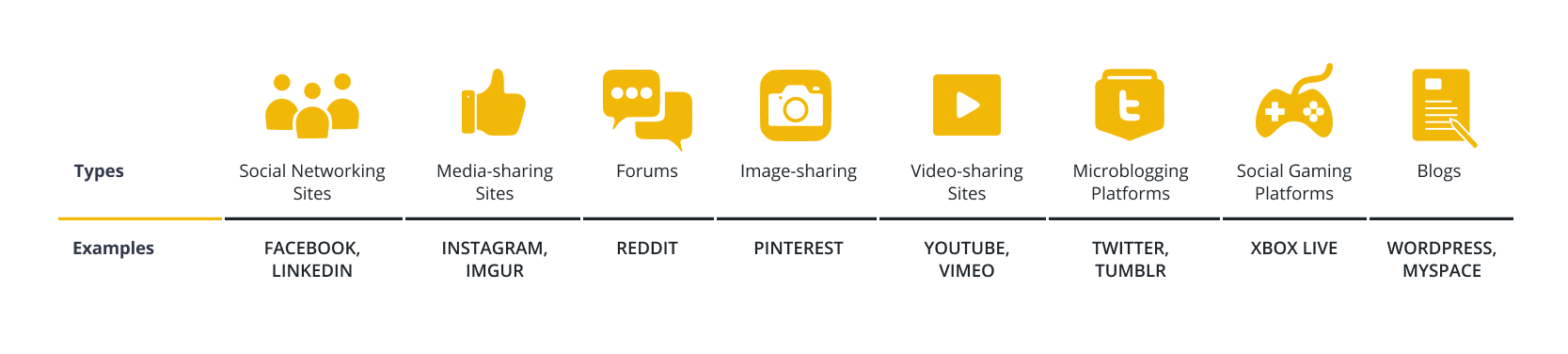
Although the image above only covers traditional platforms, you should expand your perimeter to cover other sites like:
Strategies for Effective Use of SOCMINT 🔗︎
With so much data at our disposal, it’s sometimes challenging to sift through it all to find meaningful connections and focus on what’s most relevant at a given moment in our investigation.
Here’s what you can do to harness SOCMINT effectively:
-
Broaden Your Horizon: Beyond mainstream platforms, delve into forums, blogs, and region-specific sites.
-
Prioritize Quality: Although some tools can gather substantial amounts of data, manual exploration is often necessary to uncover subtle details. A comment on a niche forum or a discussion on a lesser-known chat group can sometimes provide the most revealing insights.
-
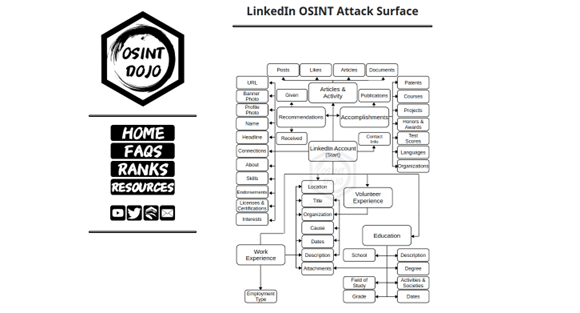
Define a Workflow: Creating a workflow for investigating specific social media platforms or specific types of information like email addresses or phone numbers helps to reduce the risk of missing vital information and ensures a standard quality of analysis across the board. I highly recommend the OSINT Attack Surface Diagrams shared by the OSINT Dojo to help you define a custom workflow for your investigations.
Source: osintdojo
To take this a step further, you can use a mapping tool that will help you combine and analyze all the data from a single interface. This is where Maltego stands out in the SOCMINT landscape, as it allows investigators to gather intelligence from a wide range of diverse sources. Maltego also streamlines tasks like deduplication, visualization, automation, and report generation, which can be beneficial when collaborating with other investigators.
Profiling Threat Actors with SOCMINT 🔗︎
Now that you have your strategy and tools in place, you can start leveraging the available SOCMINT sources that you consider relevant for your investigation. Here is a quick breakdown of how you can use them to profile threat actors:
- Profile Identification: Analysts can identify profiles or accounts associated with known threat actors or suspicious activities.
Example: A user on a forum discussing specific hacking techniques or sharing malware code snippets.
- Communication Patterns: By monitoring conversations and interactions, analysts can discern communication patterns, helping identify networks of malicious actors.
Example: Tracking interactions between suspicious accounts on platforms like Twitter or Telegram to uncover a network of collaborators.
- Sentiment Analysis: Analyzing sentiments can provide insights into threat actor’s motivations, intentions, or potential targets.
Example: A surge in negative sentiments towards a specific organization might indicate it as a potential target for hacktivist groups.
- Content Analysis: Reviewing shared content, such as images, videos, or links, can give clues about a threat actor’s capabilities, tools, or methodologies.
Example: A user sharing screenshots of a compromised system or tutorials on exploiting specific vulnerabilities.
- Temporal Analysis: Observing the timing of posts or interactions can provide insights into threat actors’ active periods, potentially revealing their time zones or operational hours.
Example: A threat actor consistently posts or interacts during a specific time, hinting at their location.
- Geolocation Data: Some social media platforms provide geolocation data, which can be invaluable in tracking the physical location of threat actors.
Example: A tweet or post with location data enabled, pinpointing a threat actor’s location.
- Network Analysis: Social media platforms are inherently about connections. Analyzing these can reveal affiliations, hierarchies, or group dynamics.
Example: Identifying followers or mutual connections of a known malicious account to uncover a broader network of threat actors.
- Trend Monitoring: Monitoring trending topics or hashtags can provide early warnings about emerging threats or campaigns.
Example: A sudden spike in discussions around a specific vulnerability or exploit.
Beyond threat actor profiling, SOCMINT has many other applications. For example, analysts can predict threats by monitoring online discussions about vulnerabilities. Social media, a hub for information warfare, can be navigated using SOCMINT to counteract disinformation campaigns. Meanwhile, early detection of employees discussing sensitive issues online allows for prompt interventions, preventing potential security breaches or issues.
Challenges in the SOCMINT Arena 🔗︎
While powerful, SOCMINT is not without its pitfalls:
- Volume Overwhelm: Every day, billions of posts, tweets, shares, and comments flood social media platforms. This massive influx of data can quickly overwhelm analysts. It’s like trying to find a needle in a haystack, but the haystack is constantly growing. Without the right tools and techniques, crucial information can be missed, or analysts can spend excessive time on irrelevant data, reducing efficiency.
- Disinformation: Not everything on social media is as it seems. Fake news, altered images, and misleading narratives are everywhere. These are often intentionally planted to mislead or divert attention. Analysts must learn to distinguish between genuine threats and decoys. Misinterpreting disinformation as an actual threat can lead to wasted resources and incorrect threat assessments.
- Ethical and Legal Hurdles: The digital world has its own set of ethical guidelines and legal boundaries. Techniques like using sock puppet accounts to gather information can be seen as deceptive or intrusive. Moreover, scraping data or accessing private information without consent can breach privacy laws and platform terms of service. Analysts must strike a balance between gathering comprehensive intelligence and respecting digital rights. Overstepping boundaries can lead to legal repercussions, damage to reputation, and potential loss of access to vital platforms.
Maltego: The SOCMINT Powerhouse 🔗︎
Maltego has emerged as a favorite tool for many analysts diving into SOCMINT. It facilitates the process by:
Maltego delivers detailed reporting ideal for stakeholder communication and further analysis. Moreover, it offers an all-in-one tool that aggregates information from diverse sources within a single interface, enhanced by its visual analysis that presents actional insights. This eliminates the need to toggle between platforms, providing users with an efficient and value-driven data analysis experience.
Conclusion 🔗︎
In the complex landscape of social media, every post, tweet, and like can be a potential lead. SOCMINT stands as a pivotal tool for cyber threat intelligence, transforming digital chatter into actionable insights. Recognizing the nuances of data, discerning genuine threats from disinformation, and navigating the ethical maze are all part of the process.
With powerful tools like Maltego, analysts can streamline the data analysis to find patterns, anomalies, and indicators that, when pieced together, reveal a comprehensive threat narrative. As cyber threats evolve in complexity, mastering SOCMINT isn’t just a recommendation, it is a must.
To learn more about using Maltego and SOCMINT in your investigations, download the handbook below.
Download the resource
Discover more resources related to Social Media Intelligence here and follow us on Twitter, LinkedIn, and Mastodon, or subscribe to our newsletter.
Happy investigating!
About the Author 🔗︎
Mario Rojas 🔗︎
Mario Rojas is a former Cyber Security and Threat Intelligence Subject Matter Expert at Maltego with more than 14 years of experience in the cybersecurity field. His expertise in open-source intelligence (OSINT) allows him to effectively map and visualize complex relationships and connections between entities, from IP addresses and domain names to social media profiles and Darkweb forums.