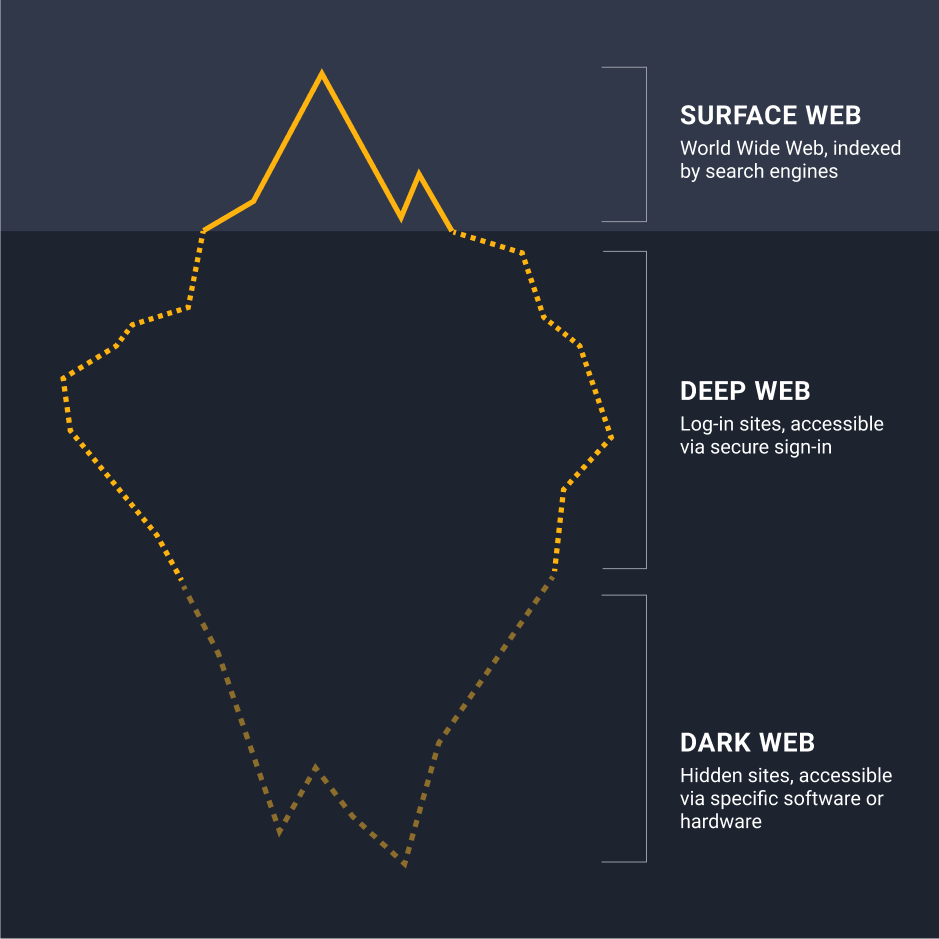
The dark web is often seen as a mysterious and impenetrable part of the internet, accessible only to cybercriminals and law enforcement. However, its hidden forums and marketplaces hold valuable information that companies can use to protect their assets and understand emerging threats. Despite the belief that dark web investigations are too complex for anyone but law enforcement, tools like Maltego are making these investigations more accessible and effective for businesses.
Understanding the Dark Web 🔗︎
The dark web is a part of the internet that isn’t indexed by search engines and requires specific software, like the Tor browser, to access. Its hidden nature makes it a hub for illicit activities and a valuable source of intelligence for those who know how to navigate it.
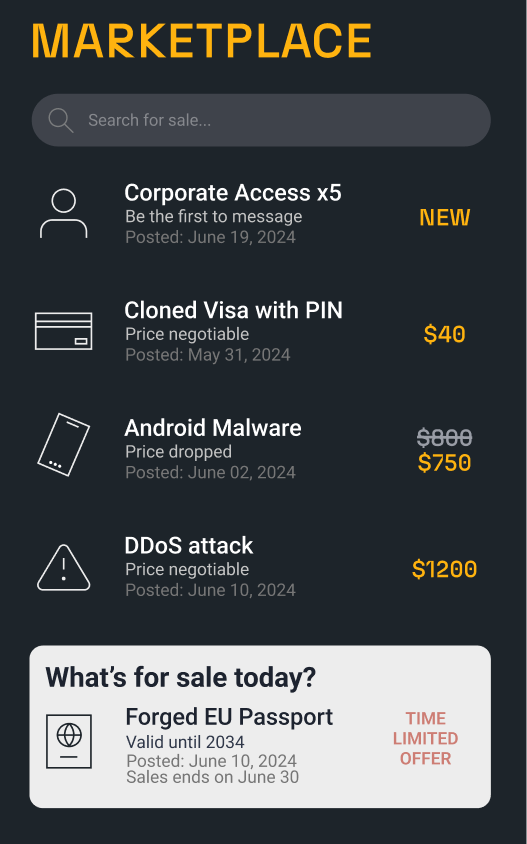
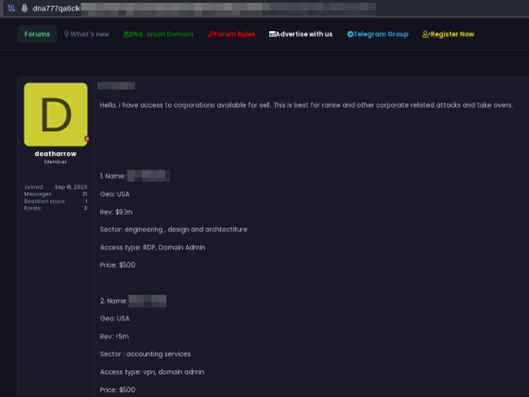
Key forums and marketplaces on the dark web are where many of these activities begin. These sites are often the starting points for trading stolen data, selling insider information, and offering access to compromised systems.
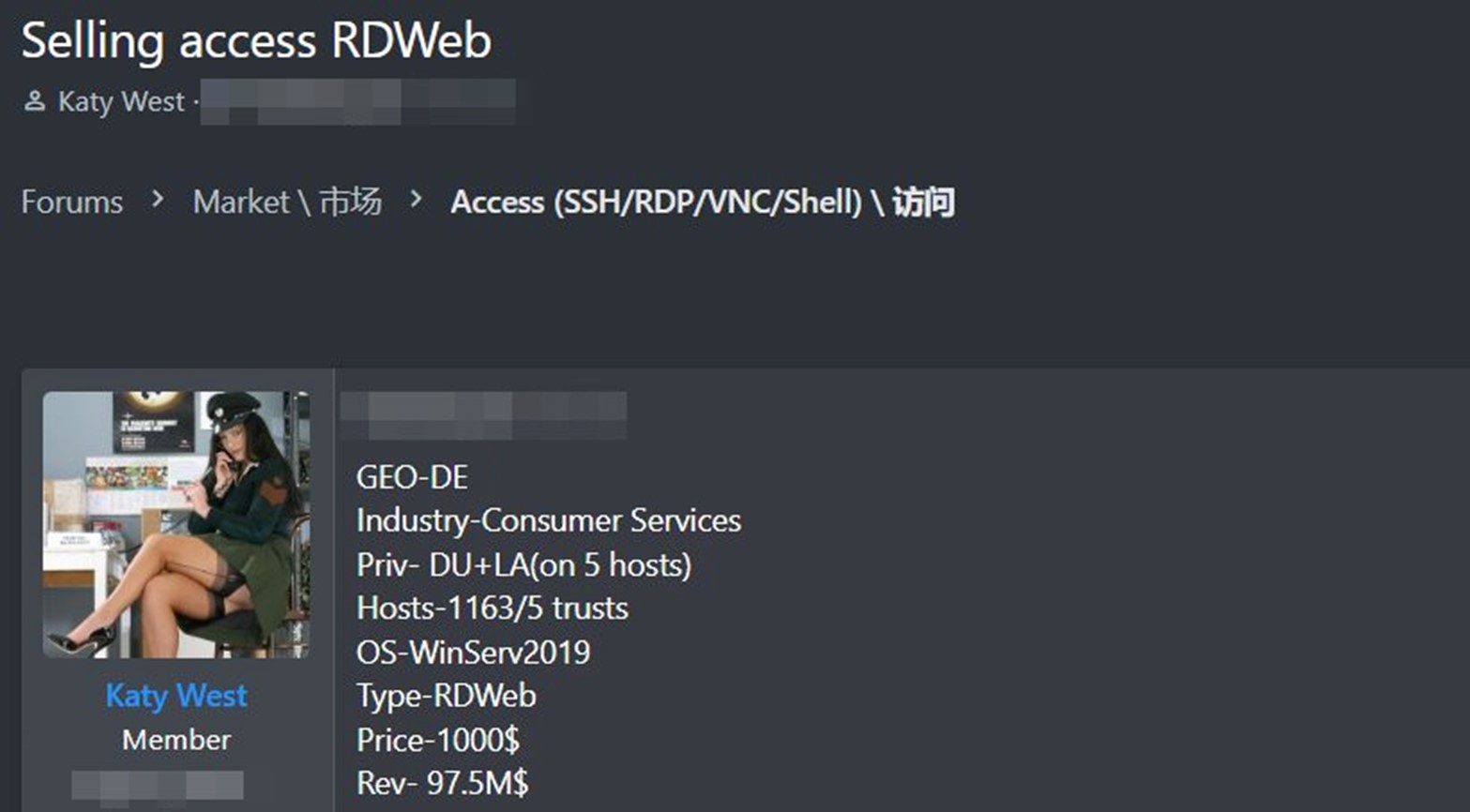
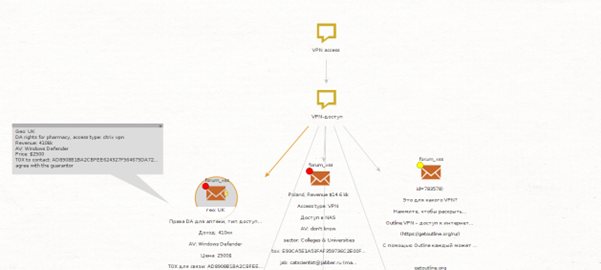
In the above example, we see a threat actor using a dark web forum to offer access to hacked instances of various organizations. For organizations aiming to protect themselves, monitoring these posts for mentions of their infrastructure is crucial.
Use Cases for Dark Web Investigations 🔗︎
Investigating dark web forums involves navigating the dark web and manually searching for specific keywords to uncover information that may be relevant to your organization. This can be daunting and risky, exposing investigators to malware, phishing attacks, and other dangers. Maltego functions as a protective barrier between the investigator and these threats, providing access to essential information without direct interaction.
INVESTIGATOR NOTE Maltego provides a layer of anonymity for users accessing data, masking their identity from external data vendors. Typically, data providers can identify users and their searches through their API keys. However, with Maltego Graph (ISO certified), we act as a middleman between the user and the diverse range of data sources. In this way, all queries first go to Maltego servers, which then forward the requests to various API providers. This ensures anonymity, particularly for law enforcement and intelligence agencies, while still offering access to the most relevant data for investigations.
Below is a practical use case demonstrating how Maltego can assist in minimizing potential business risks by proactively responding to any mentions or activity involving your organization. We will provide step-by-step guidance on where to start and how to attribute results. Continue reading!
Access Brokers 🔗︎
Access brokers are individuals or groups that sell access to compromised systems. They often operate on dark web forums, offering Remote Desktop Protocol (RDP) access, VPN credentials, and more.
-
Starting Point: A keyword relevant to the investigation.
-
Keywords: “RDP sale,” “VPN access,” “buy accounts,” “admin rights,” “server login,” “network entry.”
-
Goal: To identify key brokers and their networks for active monitoring of their activities and communication.
-
Example Scenario: A threat analyst is tasked with preparing reports that include a list of threat actors and forums likely to purchase confidential information from potential insider threats, for active monitoring and insights. Below you can find the typical workflow for this example scenario.
-
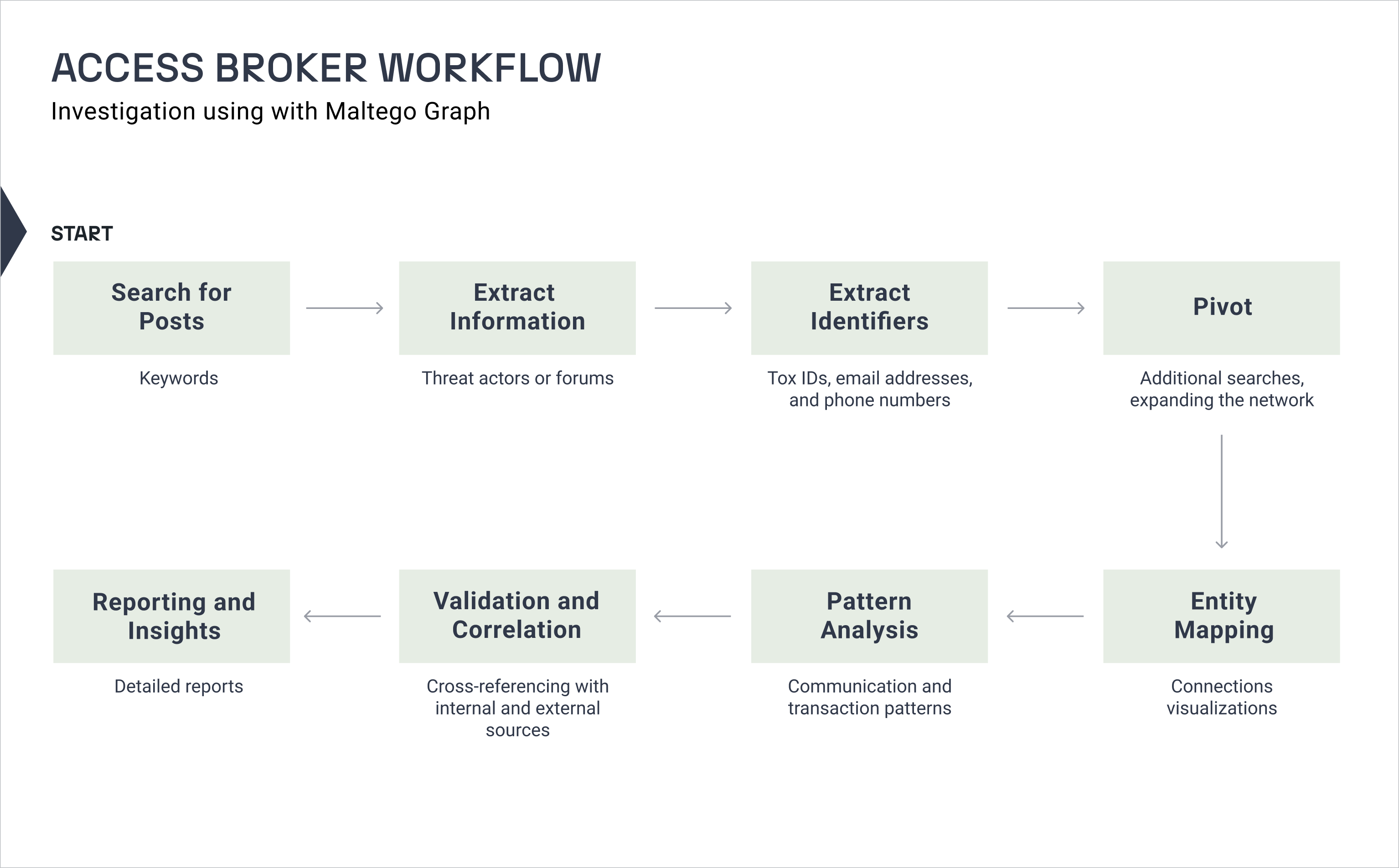
Workflow:
- Search: Use Maltego to search for posts mentioning any of the keywords mentioned above.
- Extract Information: Gather details about the threat actors and forums involved in these sales.
- Extract Identifiers: Look for other identifiers like TOX IDs, email addresses, and phone numbers.
- Pivot: Use this information to pivot into additional searches, expanding the network of connected organizations.
- Entity Mapping: Visualize connections between access brokers, buyers, and other related organizations.
- Pattern Analysis: Analyze communication and transaction patterns to identify key players and networks.
- Validation and Correlation: Cross-reference the collected data with internal threat intelligence and external sources to ensure accuracy.
- Reporting and Actionable Insights: Generate detailed reports and provide actionable recommendations based on the findings.
Let’s start our investigation by searching for a keyword related to access brokers. In the following example, a threat actor is selling access to multiple Remote Desktop hosts belonging to a German organization for only $1,000.
-
Step 1 – Starting off
- Overview: In this initial step, we will search for a keyword to determine the type and quantity of posts available. This will help us visualize the access broker’s entire network and business area.
- Task in Maltego: Add a Phrase Entity to a new Maltego Graph. Enter a relevant keyword like “RDP access.” If you are searching for posts mentioning your organization, include your organization’s name as well. For example, “RDP access maltego.”
-
Step 2 – Searching for related posts
-
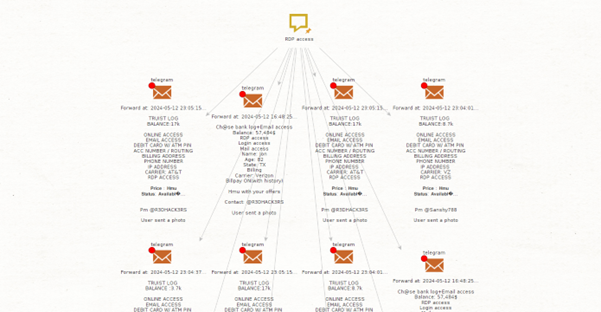
Overview: We will try to look for related posts that contain the keyword. We will use the same data source as the previous investigation.
-
Task in Maltego: Select the Phrase Entity and run the Transform:
- Find Posts Related to Phrase [Cybersixgill]
In this case, Maltego returned several Telegram posts offering infostealer logs. If you are in law enforcement, you would likely appreciate that this provides numerous posts with contact information.
-
-
Step 3 – Reporting for mentions
-
Overview: If your company is mentioned in any of the posts, immediately take steps to secure the affected accounts, notify relevant stakeholders, and investigate the extent of the breach to mitigate further risks.
**INVESTIGATOR NOTE** It's important to remember that cybercriminals often operate in their native languages. Some of the most prolific dark web forums are tailored to Russian-speaking individuals. However, you can still use Maltego to search for posts in other languages, even if you don't speak the language.
-
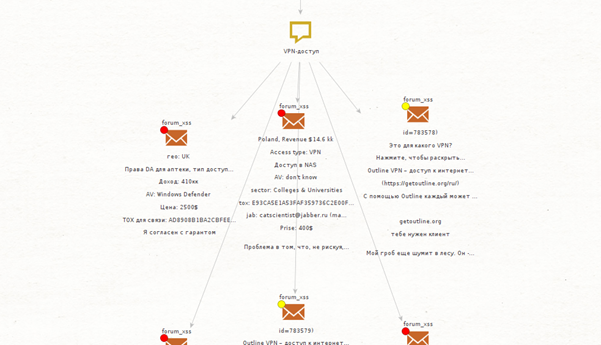
Considering that access brokers operate globally and that many dark web forums target Russian-speaking individuals, let’s search for posts where access brokers offer VPN access on the dark web, specifically written in Russian.
-
Step 1 – Starting off
-
Overview: Just like before, let’s add a Phrase Entity into a new graph and enter “VPN access”, but this time we will use the DeepL Transforms to translate the phrase into Russian before moving on to the Darkweb Transforms. You can modify the Phrase Entity to include your organization’s name.
-
Task in Maltego: Run the Transform below and put the target language as “RU.”
-
-
Step 2 – Searching and translating related posts
-
Overview: Then, we will try to look for related posts that contain the Russian keyword. And then we will translate the interesting posts back to English to see what they are about.
-
Task in Maltego: Run the same Transform as previous steps to look for related posts and use DeepL to translate the selected posts back to English to facilitate the research.
-
As before, if your company is mentioned in any of the posts, immediately take steps to secure the affected accounts, notify relevant stakeholders, and investigate the extent of the breach to mitigate further risks.
Please note that access brokers are known not only for selling access to compromised hosts but also for offering to buy access from other threat actors and even willing individuals who may work for potential victims (insider threats).
Check Out the Full White Paper for Insights on Dark Web Investigation 🔗︎
By integrating the workflows with Maltego’s capabilities, organizations can conduct thorough dark web investigations, uncover critical insights, and take proactive measures to enhance their security posture. In our white paper, we outline workflows for five additional use cases where you can benefit from utilizing Maltego for dark web investigations:
- Insider Threats
- Data Breach Detection
- Counterfeit Goods and Intellectual Property Theft
- Fraud and Scam Detection
- Threat Actor Profiling
Early detection is crucial in mitigating exposed assets and data, as well as preventing further information leaks. By enabling quick responses to such threats, organizations can significantly reduce their risk and protect their valuable information. Maltego’s powerful capabilities for dark web investigation play a vital role in this proactive approach, ensuring that threats are identified and addressed promptly to maintain a robust security posture.
Download the white paper to learn what types of dark web investigations you can conduct using Maltego!
Download the resource
Stay connected with us on X and LinkedIn, and subscribe to our email newsletter to get updated with the latest news and developments.
Happy Investigating!
About the Author 🔗︎
Mario Rojas
Mario Rojas is a former Cyber Security and Threat Intelligence Subject Matter Expert at Maltego with more than 14 years of experience in the cybersecurity field. His expertise in open-source intelligence (OSINT) allows him to effectively map and visualize complex relationships and connections between entities, from IP addresses and domain names to social media profiles and dark web forums.