In the evolving landscape of modern societies grappling with climate change, terrorism, and cyberattacks, the most significant challenge we face is adapting to a rapidly growing information ecosystem, largely driven by the internet and social media networks.
Especially in the digital information sphere, the message can be easily amplified or modulated, leading to a dangerous influence that may manipulate simple opinions into facts. Disinformation and misinformation have become increasingly significant issues, causing greater polarization in our democracies and fueling the radicalization of individuals.
Who benefits from this chaotic landscape? Extremist groups seem to be seizing the chance, exploiting the widespread misinformation to radicalize individuals with ideologies. With its vast and intricate network, the internet is not only a medium for communication but a breeding ground for radical ideologies.
In this whitepaper, we will map out the digital footprint, comprehensive networks, strategies, and operational methods of one of these extremist groups called “Involuntary celibates (Incels)” who believe they are entitled to a relationship with a woman, but they are incapable of finding a partner. Multiple acts of extreme violence and even murder have been attributed to this group.
To gain a better understanding of incels, there are two highly recommended resources to explore:
- Incels: A Guide to Symbols and Terminology
- Incels: A First Scan of the Phenomenon (in the EU) and its Relevance and Challenges for P/CVE
Before we explore this group, let’s first understand the discipline of threat assessment.
What is Threat Assessment? 🔗︎
Threat assessment is the practice of determining the credibility and seriousness of a potential threat, such as the one posed by extremist groups, as well as the likelihood of these threats becoming reality. According to J. Reid Meloy, Ph.D., the discipline…
…aims to interrupt people on a pathway to commit predatory or instrumental violence, the type of behaviour associated with targeted attacks”
J.Reid Meloy, Ph.D., co-editor of International Handbook of Threat Assessment (2013)
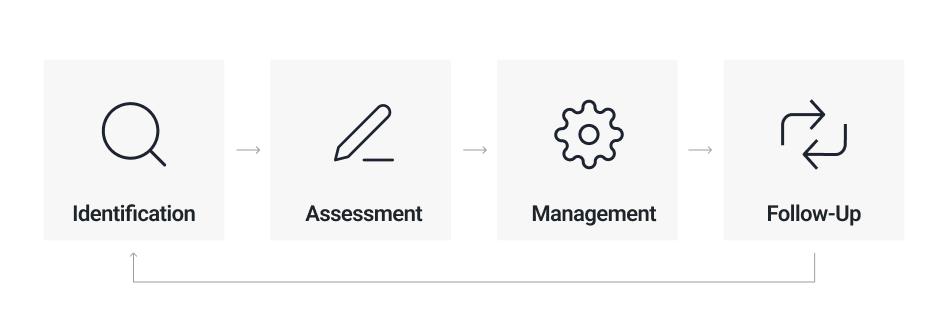
Threat assessment comprises the following key components:
- Identification: Identifying threats to commit a potentially unfavorable act
- Assessment: Determining the seriousness of the threat
- Management: Developing intervention plans to address the underlying issue
- Follow-up: Continuous assessment and Safety Planning
Investigate Involuntary Celibates (Incels) 🔗︎
In this whitepaper, we provide a detailed exploration of the world of incels, offering insights into how to assess the threat landscape and identify their networks, infrastructure, and operational methods using Maltego.
For the demo, we used Maltego Data Pass: Person of Interest along with several Transforms to investigate the community’s dynamics:
- Maltego Standard Transforms
- Maltego News Transforms
- Maltego Dorking
- WhoisMXL API
- DomainTools Enterprise
- Tisane Labs
Understanding and dismantling these networks is a critical step in protecting vulnerable individuals from radicalization and preventing acts of violence and hate inspired by such radical groups. This information is invaluable, especially for law enforcement agencies, governmental bodies, and other organizations, such as anti-hate NGOs in developing targeted strategies to counteract and prevent the incidents.
Download this whitepaper about counteracting radicalization and the spread of extremist groups and learn how to conduct your own threat assessment now!
Download the resource
Don’t forget to follow us on Twitter, LinkedIn, and Mastodon or subscribe to our email newsletter for more whitepapers, case studies, and investigation tips like this!
Happy investigating!
About the Author 🔗︎
Carlos Fragoso
Carlos is the Principal Subject Matter Expert and Lead Instructor at Maltego with over 20 years of professional experience in information security: Incident response, digital forensics, threat intelligence, and threat hunting. A curious and passionate investigator working with big companies and LEAs to tackle cybercrime around the world (Europe, Middle East, LATAM) SANS Institute Instructor.