Uncovering Information on a Dark Web Gun Seller 🔗︎
Dread can be considered the Reddit of the Dark Web and, just like Reddit, it is subdivided into different sub forums known as subdreads. The subdread named [/d/murderhomelesspeople] is the sub forum where drug dealers (or people pretending to be one) discuss their different experiences.
In this whitepaper, we will investigate the persona of “scaryred24,” an individual who offered a gun for sale in a thread posted to this subdread.
Chancing Upon Scaryred24 🔗︎
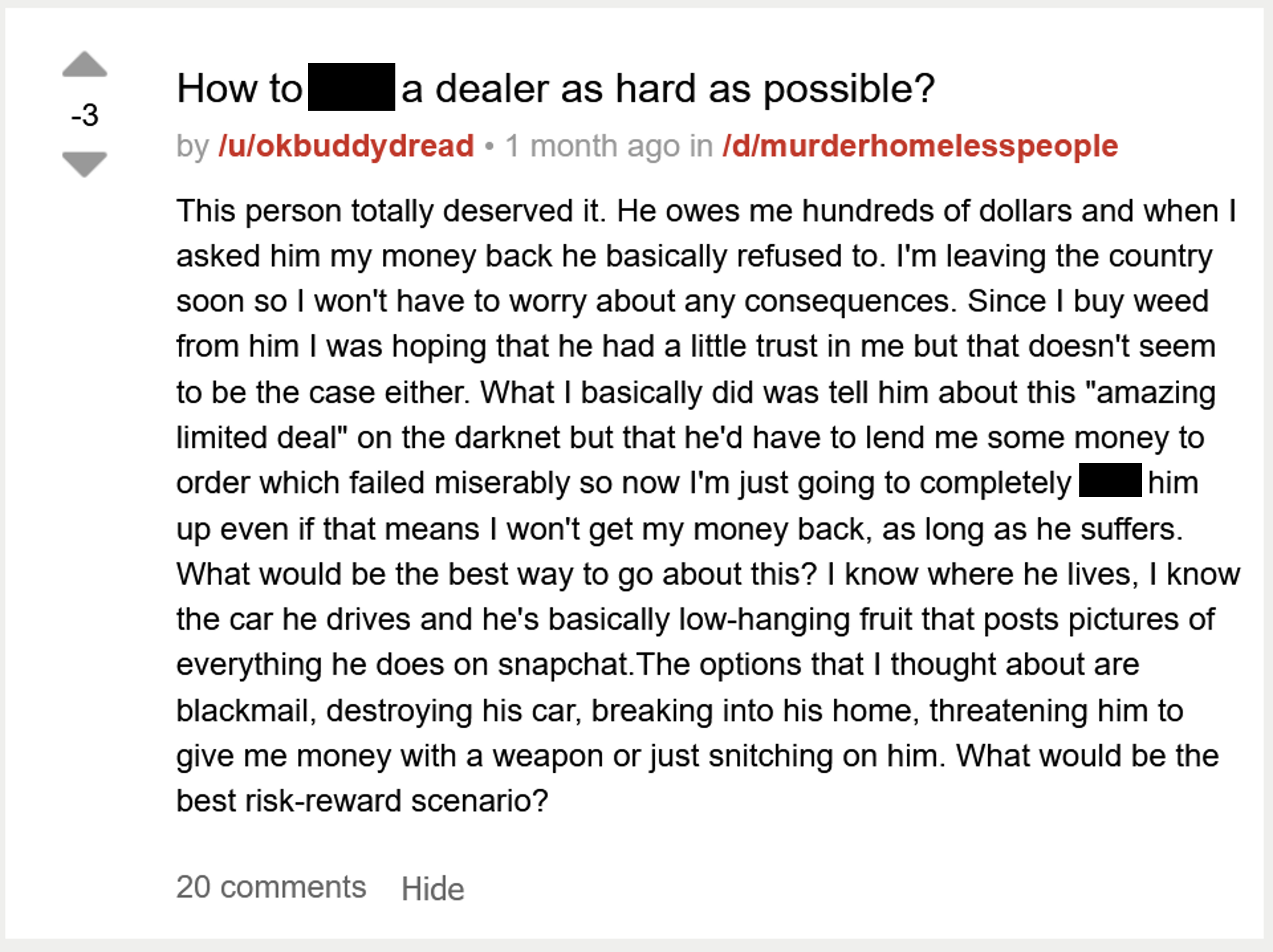
The image below shows the Dread post found on the onion site Dread[^1]. The post, made by the user “okbuddydread” around October 2021, notes that they want to take revenge against their drug dealer who allegedly owes them money.
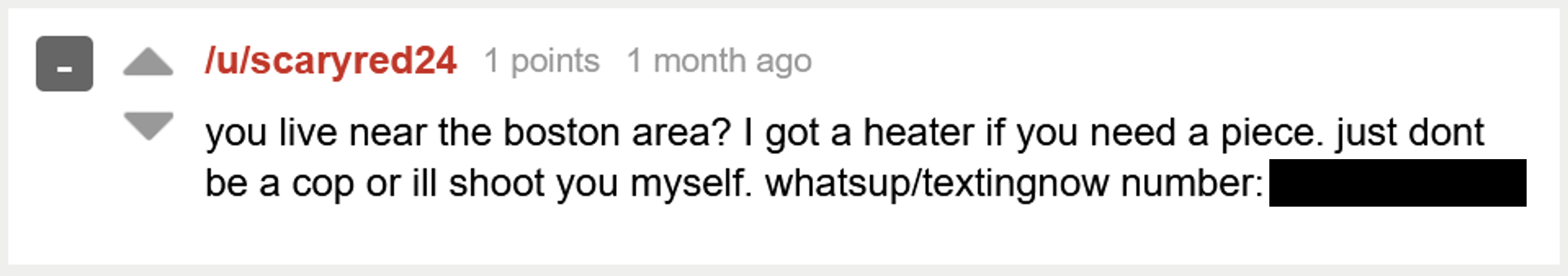
Amongst the 20 comments added to this post, we found one comment by the user scaryred24, who offers to sell a gun to “okbuddydread.”
At this stage, it is already possible to gather significant information from these posts. To begin with, the username “scaryred24” seems quite unique. And, given that scaryred24 offers to sell a “piece” (firearm) to the poster if they are in or around the Boston area, it can be assumed that they are located somewhere within that area. Lastly, “scaryred24” has also provided a phone number on which they can be contacted via WhatsApp or text.
This information already provides a good start to an investigation. The different pieces can be used as starting points to see what kind of information we could gather to unmask the person hiding behind the user “scaryred24.”
Download Whitepaper 🔗︎
Access the whitepaper below to get a full overview of the investigation, the steps you can replicate in Maltego, and other investigator tips for person of interest investigations.
Download the resource
We hope this whitepaper will help you collect relevant intelligence and find online traces of your darkweb persona in Maltego.
For more investigations like this, you can check out our other resources:
- Investigating the Alleged Leak of FSB Agents’ Phone Numbers
- Pattern of Life Analysis with Maltego
- Unmask Cybercriminals’ Real Identities with Constella and Maltego
Don’t forget to follow us on Twitter and LinkedIn and sign up to our email newsletter, so you don’t miss out on updates and news!
Happy investigating!
About the Author 🔗︎
Mathieu Gaucheler Mathieu Gaucheler is a Subject Matter Expert at Maltego. His responsibilities include research-driven content development for blog posts, webinars, and talks. He started working in cybersecurity in Barcelona, focusing on malware analysis and sandbox development. He has previously presented his research at BotConf and RSA APJ.