Anonymity is not a choice for investigators – it’s a necessity. The reasons extend far beyond personal safety and weave into the very fabric of successful investigative work.
In this guide, we focus on the dangers of exposure when investigating fraud or conducting corporate investigations for the investigators, the company they work for, the clients they serve, and the success of their investigations.
In the later part, we will share a cheat sheet that outlines the measures that each investigator should take to protect themselves and their organization when using OSINT and explain how Maltego can help maintain anonymity throughout the entire operation.
Table of Contents 🔗︎
Consequences of Data Exposure on the Entire Operation 🔗︎
The internet never forgets, and retracting shared information is practically impossible. Compromising an investigator’s identity or revealing that a target is under scrutiny can affect operations that could be ongoing for weeks or months.
The Domino Effect of Exposure 🔗︎
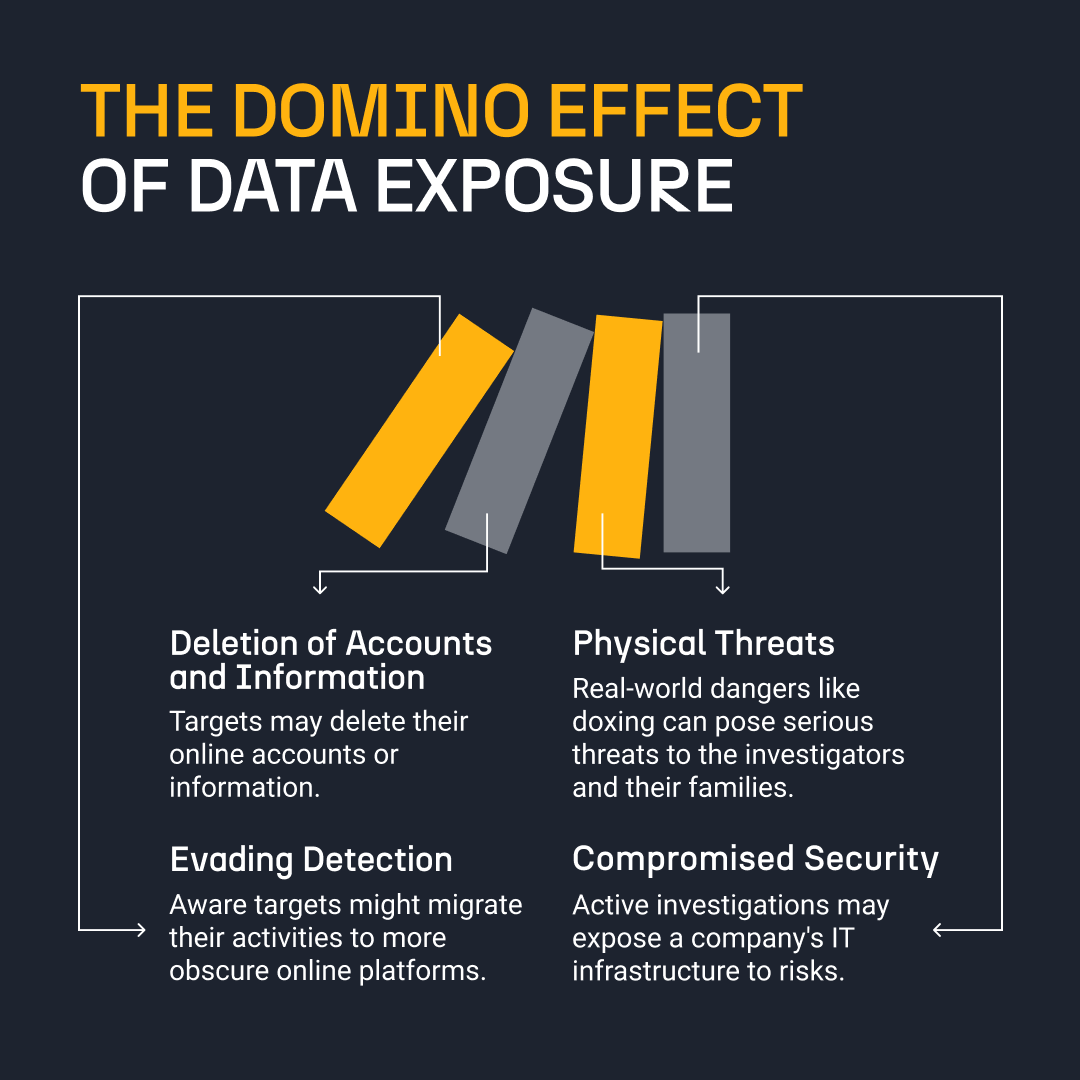
When adversaries become aware they are being monitored, their responses can lead to serious consequences.
- Evidence Tampering and Loss
When bad actors realize their activities or accounts are under scrutiny, their immediate reaction often involves erasing their digital footprints. This can range from deleting incriminating accounts and information to moving their operations to more underground or obscure online spaces, or even offline. This hampers investigations and risks the loss of crucial evidence, particularly if it hasn’t been adequately preserved through downloads, screenshots, or other means.
- Physical Threats to Investigators
Beyond digital threats, there have been doxing incidents targeting employees involved in fraud management, brand investigations, and similar fields.
- Compromised Company Security
Engaging with websites or sources riddled with malware or other privacy-intrusive technology without adequate precautions can lead to the compromise of sensitive company data. This not only affects the investigative team, but also jeopardizes the security of the company’s entire infrastructure and its clients or partners.
There are tried-and-true measures you can take to maintain anonymity at each stage of your investigation. Download your cheat sheet with do’s and don’ts for every investigator now.
Common Data Exposure Scenarios You Should Avoid 🔗︎
Investigating the roots of data exposure reveals a mix of factors stemming from an inadequate toolkit, insufficient policies and best practices, and a lack of training or awareness. Even simple complacency, leading to sloppy habits and time pressure, can contribute to these vulnerabilities.
Each of these elements, in isolation or combined, can inadvertently open the door to exposing your identity or revealing information about your company. Let’s look at some examples.
Social Media Oversights:
- Scenario: Inadvertently alerting the person of interest when investigating them on social media.
- Cause: Using a personal or easily traceable account instead of a carefully managed sock puppet account.
- Example: Viewing a person of interest’s profile on platforms that notify users of profile visits can lead to exposure or accidental interactions like following or liking a post can raise alarms.
Web Browsing Vulnerabilities:
- Scenario: Accessing unknown websites. A mere URL access can reveal an investigator’s IP address and other digital footprints.
- Cause: Insufficient use of secure browsing tools and techniques that leads to exposure of device ID, system name, geolocation, and browser details.
- Example: Without proper safeguards, visiting a new forum or website might result in cookies tracking the investigator.
Process and Technology Gaps:
- Scenario: Inadequate processes and technology used that create vulnerabilities during investigations.
- Cause: Lack of proper protocols for new or unfamiliar digital environments can lead investigators to improvise, increasing the risk of exposure.
- Example: Encountering a new type of online platform without a predefined approach can lead to insecure browsing practices.
Human Error and Complacency:
- Scenario: Common investigator lapses or oversights.
- Cause: Complacency, time pressure, or lack of awareness can result in careless actions.
- Example: Liking an old photo of a target, even using a sock puppet account that signals to the target that they are under surveillance.
INVESTIGATOR TIP: With Maltego, you remain anonymous at all times, and there is no need to set up a sock puppet since Maltego acts as a proxy. This ensures your identity is protected at every stage. For high-profile investigations, you can use a stealth mode that completely restricts the desktop client from downloading data or information directly from the internet. We will explain this in the later part of this article.
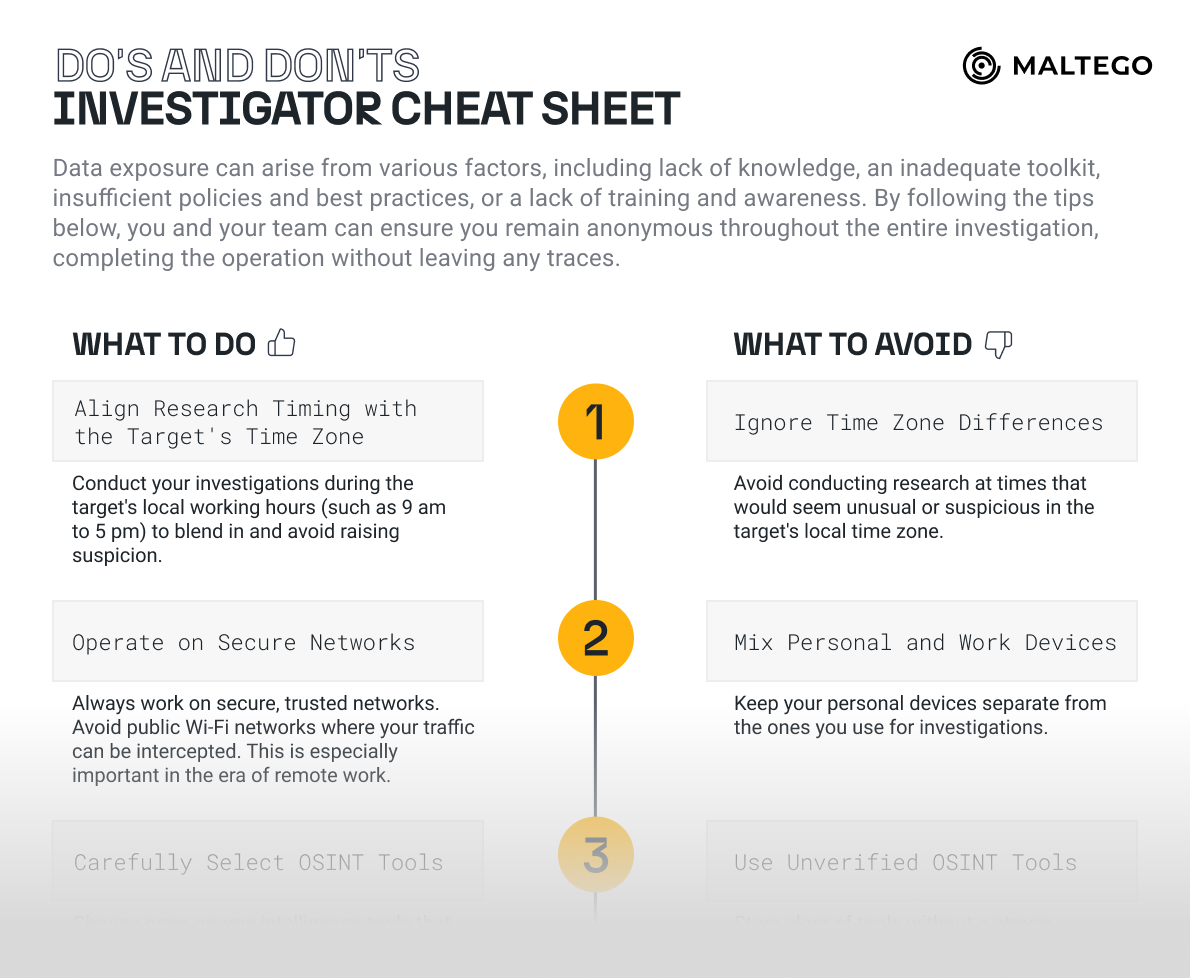
Do’s and Don’ts for Every OSINT Investigator to Maintain Anonymity 🔗︎
To avoid those compromising situations, fraud and threat analysts can adopt several reliable measures. Here’s just a couple of do’s and don’ts for you:
Do This When You Run an Investigation 🔗︎
- Align Research Timing with the Target’s Time Zone: Conduct your investigations during the target’s local working hours (such as 9 am to 5 pm) to blend in and avoid raising suspicion.
- Operate on Secure Networks: Always work on secure, trusted networks. Avoid public Wi-Fi networks where your traffic can be intercepted. This is especially important in the era of remote work.
- Carefully Select OSINT Tools: Choose open-source intelligence tools that are known for their reliability and security to reduce the risk of exposing your digital footprint.
- Use a Paid VPN for Web Research: Employ a reputable Virtual Private Network (VPN) to mask your IP address, especially when researching websites. This step is crucial to prevent website owners, including potential targets, from tracking your visit back to you.
Don’t Do This When You Run an Investigation 🔗︎
- Ignore Time Zone Differences: Avoid conducting research at times that would seem unusual or suspicious in the target’s local time zone.
- Mix Personal and Work Devices: Keep your personal devices separate from the ones you use for investigations.
- Use Unverified OSINT Tools: Steer clear of tools without a strong reputation for security, as this can lead to data leaks or digital footprint exposure.
- Rely on Free VPNs or Skip VPN Usage: If possible, don’t ever run an investigation without a VPN as this can leave your IP address exposed to website owners and potential targets, especially during website investigations. Ideally, you should also avoid free VPNs as they are easier to spot and might alert your target that someone trying to obscure their location is investigating them.
These tips are just a few key examples of how you can maintain your anonymity during an investigation. We have prepared a separate 4-page-long cheat sheet with do’s and don’ts for you, which is tailored to every investigator. Make sure to download your free copy and share it with your team!
Conduct Investigations Securely with Maltego 🔗︎
In your quest to maintain full anonymity, you may choose to restrict your investigation to a single platform that can support you in avoiding the common exposure scenarios we described earlier. With Maltego, you can address the need for anonymity through several essential features.
Secure Environment for OSINT Investigations 🔗︎
Maltego allows investigators to probe social media profiles and online content without creating sock puppet accounts or risking exposure through personal accounts. It does this by querying platforms and aggregating the data in a secure sandbox environment.
This setup enables investigators to analyze content, such as translating posts or extracting images, without directly opening someone’s profile and webpages on a browser.
Transform Queries and Data Privacy 🔗︎
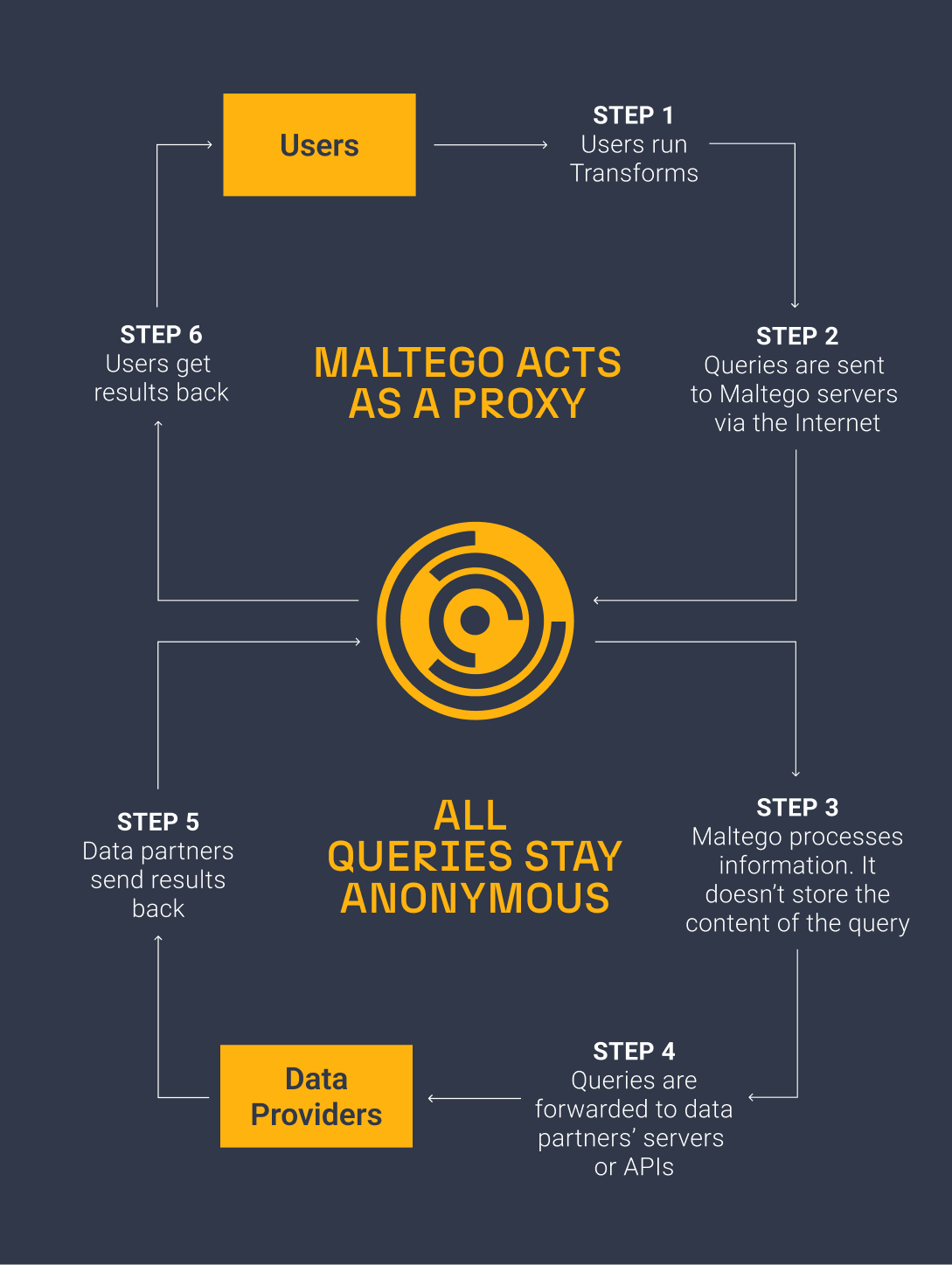
While investigating with Maltego, you will retrieve results from a given start or pivot point using the so-called Transforms to discover new connections that will help you carry out the next step in your investigation.
As you deal with sensitive cases and use internal data, the tool does not store details of the user’s Transform queries, ensuring that the investigator’s identifiable information remains concealed during data mining from public OSINT sources or online intelligence databases.
Privacy Modes 🔗︎
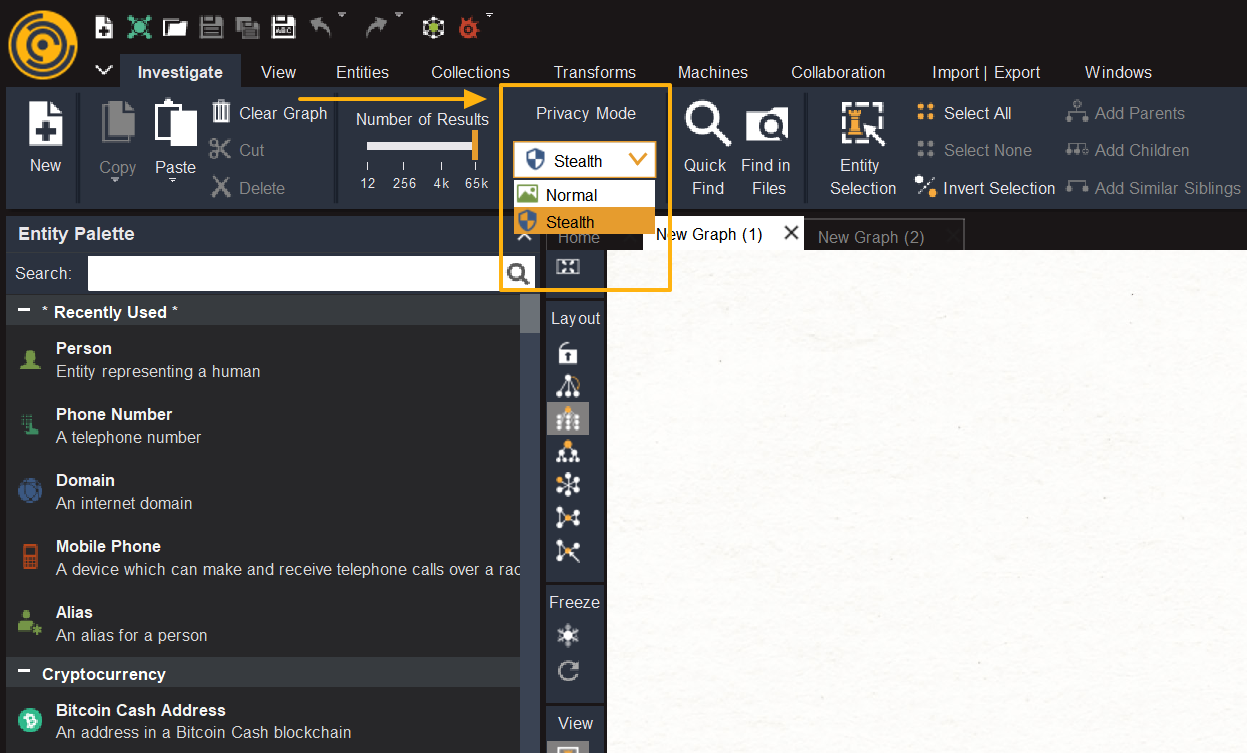
If you wish to take even more precautions, you can go one step further and switch between the two privacy modes in Maltego:
- Normal Mode: In this mode, the Maltego Desktop Client can fetch certain data types directly from the internet. While generally safe, this method might expose the user’s IP address in the target’s traffic log, which could be a concern when investigating sensitive targets.
- Stealth Mode: This mode ensures a higher level of confidentiality by preventing the desktop client from directly downloading data from the internet. This restriction includes blocking the fetching of website images or overlays. It’s recommended for situations requiring strict confidentiality or when there is concern about IP exposure. However, even in stealth mode, Transforms might contact the target via the public CTAS server or the user’s computer.
Download Your Cheat Sheet 🔗︎
There can still be situations where you might need to use a browser. This is why we recommend using Maltego in combination with other best practices, as outlined in the cheat sheet we prepared for you. If you haven’t already, you can download it now.
Download the resource
Step-by-step Investigations with Maltego 🔗︎
Now that you understand how Maltego can help you remain anonymous during an investigation, your next step should be to explore hands-on how Maltego can assist in your daily work. To do that, check out this step-by-step guide on automating your brand protection using Maltego Machines to speed up repetitive steps in your investigation conducted in Maltego.
If you are also interested in seeing how Maltego can be practically used to track down individuals responsible for online counterfeit sales, don’t miss the opportunity to watch this webinar demo recording.
Don’t forget to follow us on Twitter, LinkedIn, and Mastodon, and sign up to our email newsletter, so you don’t miss out on updates and news!
Happy investigating!