Today, we are introducing the Cybersixgill data integration in Maltego that offers investigators the ability to covertly access closed sources and critical intelligence from the criminal underground.
What is Cybersixgill? 🔗︎
Powered by the broadest automated collection from the deep, dark, and clear web, Cybersixgill is a fully automated threat intelligence solution that helps organizations protect their critical assets, reduce fraud and data breaches, protect their brand, and minimize their attack surface. It delivers contextual threat intelligence in real-time that is highly accurate, comprehensive, and covert.
Integrating Cybersixgill’s extensive data with Maltego empowers users with contextual and actionable insights, and the ability to display it in Maltego’s graphical link analysis. Threat intelligence and SOC analysts, incident responders, and other cybersecurity teams will also be able to conduct dark web investigations to obtain a visual understanding of their threat landscape and accelerate incident response – in real-time.
How Can I Start Using the Cybersixgill Transforms in Maltego? 🔗︎
In order to use Cybersixgill, you need a Cybersixgill Client ID, Cybersixgill Client Secret as well as a commercial Maltego license.
There are three ways to access Cybersixgill data within Maltego:
- Enterprise Data Allowance: As a Maltego Enterprise user, you can access and install the Cybersixgill Hub item in the Maltego Desktop Client and directly try out the data. Each Enterprise user has the allowance to run 10 Cybersixgill Transforms per month for free.
- Data Subscriptions: You also have the option to purchase a data subscription for Cybersixgill on a subscription basis in the Maltego webshop. Data subscriptions start at 250 Transform runs per month.
- Bring Your Own Key: If you are an existing Cybersixgill customer, reach out to your contact person at Cybersixgill to gain access to the Hub item. If you are not yet a Cybersixgill customer, please reach out to Maltego using the contact form here.
What Type of Information Can I Get from Cybersixgill? 🔗︎
Analysts can begin their investigations using Cybersixgill and Maltego with an Alias, URL, Hash, Domain, or IPv4 Address. From there, investigators can run Transforms to uncover information related to:
- Domains
- IP Addresses
- Intel Item Posts
- Threat Actors
- Threat Sources
- URLs
- Mentioned Hashes
Use Case: Threat Actor Profiling 🔗︎
One of the use cases of a typical investigator is to profile different threat actors that are involved in malicious activities against an organization, or ones that might pose a threat. Combining the intelligence of Cybersixgill with other Transforms will enable investigators to get a comprehensive picture about that actor. In this case, we are interested in learning more a threat actor that administers a forum where leaked databases are shared and swapped.
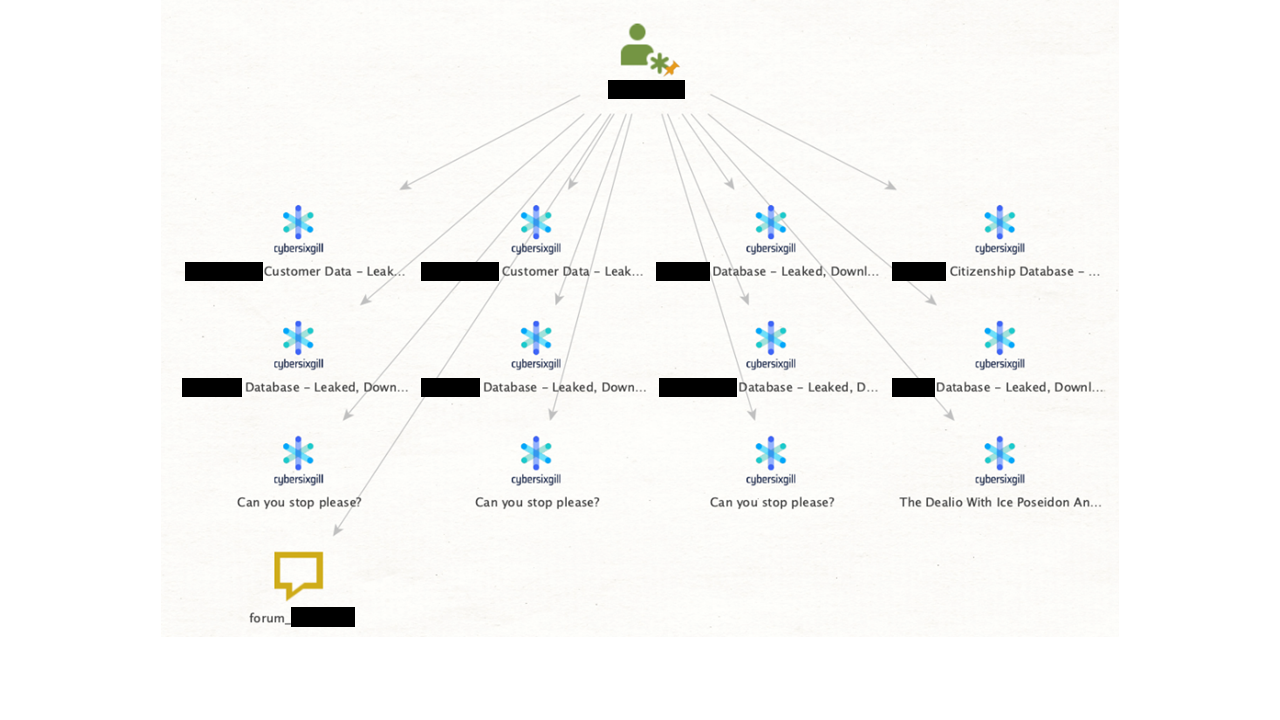
Our starting point will be an Alias Entity with our threat actor’s name. To learn which forums and other potentially criminal places this threat actor is active, we can run the To Threat Source [Cybersixgill] Transform.
Our result tells us that our threat actor only appears to be active on the forum on which they are an admin. To learn more about our threat actor’s activity on the forum, we can run the To Intel Item Post [Cybersixgill] Transform. This will return to us the names of threads on which our threat actor has authored posts.
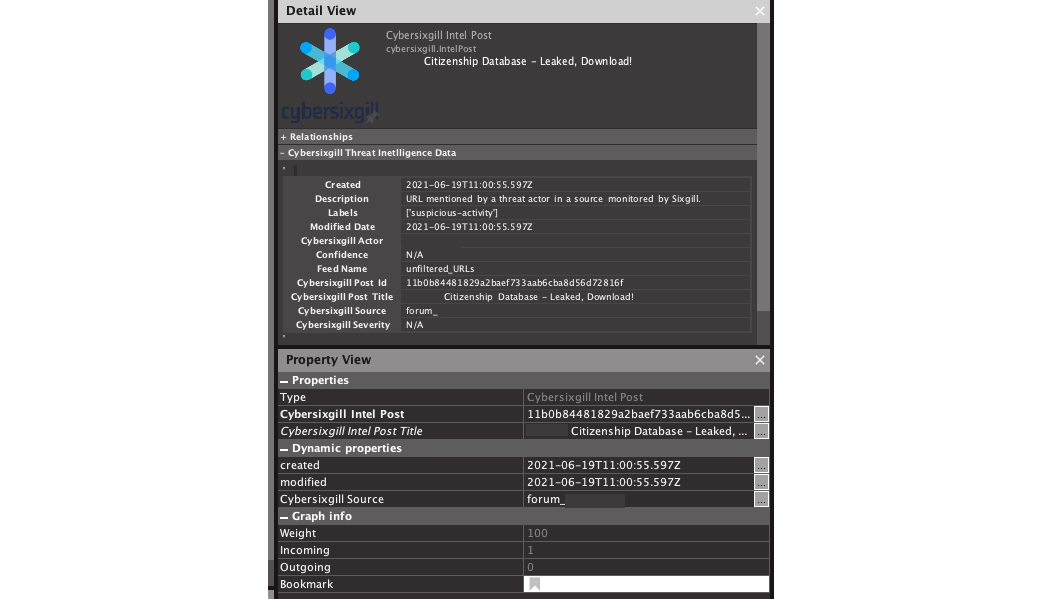
We can learn more about these posts in the Detail View and Property View within Maltego. Information here can help add context to our investigation. Users with access to Cybersixgill’s investigative portal will also be able to further explore information such as threat actors or post IDs there.
For instance, if we are interested in learning more about this thread in which a database of information related to the citizens is allegedly being shared, we can see that the post was authored on June 19, 2021.
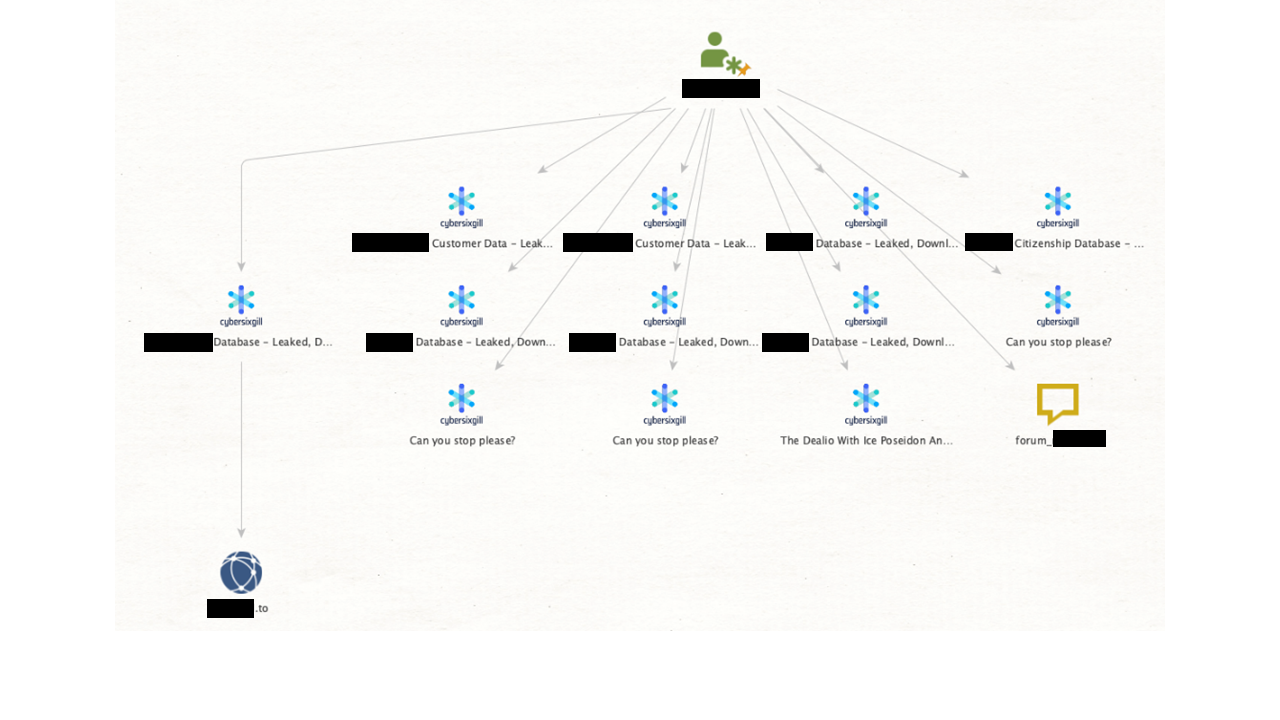
Cybersixgill provides investigators with the powerful capability to search within Intel Item Posts for critical information such as IP addresses, hashes, and more. We will select all the Intel Item Posts on our graph and run the To Domains [Cybersixgill] Transform. This will return to us domain Entities that are mentioned within the Intel Item Posts.
In this case, it returns one domain Entity, another English-language forum that hosts a myriad of criminal activity. It appears that a threat actor is sharing a compromised database of information from said rival forum.
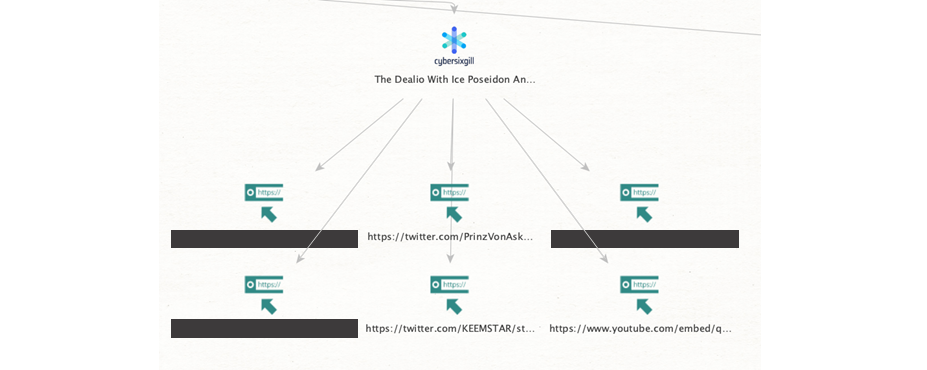
We can also run the To URLs [Cybersixgill] Transform to see mentioned URLs within our Intel Item Posts.
We get various results. Many of them are URLs pointing to other places on the same forum: this may be when a threat actor tags another forum member in a post or posts a link to another thread. We also see results from Twitter, YouTube, and GitHub.
Start Using the Cybersixgill Transforms to Accelerate Your Criminal Underground Investigations in Maltego! 🔗︎
We hope you enjoy the release of the Cybersixgill data integration for Maltego.
Don’t forget to follow us on Twitter and LinkedIn and sign up for our email newsletter to stay updated on the latest news, tutorials, and events.
Happy Threat Hunting!