Given the relentless evolution of cyber threats, organizations face constant pressure to stay ahead of emerging threats. Decision-makers depend heavily on accurate and actionable threat intelligence reports to safeguard their assets and ensure business continuity through informed decision-making.
Consequently, they expect their Cyber Threat Intelligence (CTI) teams to produce more frequent and vigilant reports, including comprehensive monthly and quarterly threat analysis reports and daily bulletins that update on threat actors and phishing attempts. These reports are essential; serving as a critical bridge between raw data and strategic action, turning complex information into clear insights that guide security efforts. In this blog, we’ll focus on how to create actionable threat intelligence reports during the dissemination stage of the intelligence lifecycle. We’ll start by examining the importance of these reports for organizations and how they drive effective decision-making.
The Importance of Threat Intelligence Report 🔗︎
Given the increasing demand for actionable threat intelligence reports in many organizations, the accuracy and value of these reports have become key indicators of a CTI team’s effectiveness. This underscores the vital role they play in organizational security and strategic decision-making.
Therefore, CTI teams have adapted to meet the increasing demands of their organizations. Much like skilled journalists, they gather and analyze extensive information - particularly from diverse data sources - to cross-reference and validate potential threats. Moreover, they must possess the ability to present their findings in well-structured, comprehensive reports.
However, challenges in creating these reports can arise at any stage of the intelligence lifecycle, from data collection to analysis. But we all can admit that challenges in the earlier stages of the lifecycle, such as collection and analysis, are another big topic for another day.
A well-crafted threat intelligence report is more than just a collection of data; it’s a strategic tool that helps organizations understand the nature of the threats they face, prioritize their responses, and allocate resources effectively. For threat intelligence teams, the ability to produce these reports is not just about technical expertise; it’s about delivering the right information in the right way to support different stakeholders in protecting the organization.
Continue reading to discover the challenges threat analysts encounter during the dissemination phase, the essential components that make reports actionable, and how to turn gathered intelligence into strategic decision-making tools!
Key Challenges Faced by Cyber Threat Analysts In Reporting 🔗︎
Even the most skilled threat intelligence teams can face challenges when creating reports during the dissemination phase that are both actionable and relevant to decision-makers. Here are some of the most common challenges:
- Lack of Standardized Guidance: Without clear guidelines or standardized formats, reports can vary significantly in structure and content. This inconsistency can lead to confusion, making it difficult for decision-makers to rely on the intelligence provided. A lack of uniformity may result in reports that are either too detailed, overwhelming the reader, or too vague, missing critical insights.
- Lack of Process: When there is no established process for creating and reviewing threat intelligence reports, teams often struggle with inefficiencies and miscommunication. A well-defined process ensures that everyone on the team understands their role and the expectations for the final product. Without this, reports can suffer from delays, gaps in critical information, and lack of coherence.
- Lack of Training/Knowledge on Creating an Actionable Report: Creating a report that drives action requires more than just compiling data; it demands analysis, insight, and a clear understanding of the audience’s needs. Team members lacking training in these areas may produce reports rich in data but poor in actionable recommendations. This knowledge gap can undermine the report’s value, leading to missed opportunities for proactive defense.
- Manual Process and Inefficiency: Manual data collection and analysis are both time-consuming and prone to errors. These inefficiencies can delay the delivery of reports, reducing their relevance and impact. Moreover, the manual process can lead to inconsistencies in how data is handled and interpreted. Automating parts of the report generation process with a tool like Maltego Graph can help mitigate these issues, allowing teams to focus on analysis and strategy rather than data wrangling.
Although tackling these challenges could fill an entire paper, we’ve compiled a few key insights into this whitepaper specifically for CTI team leads to address common issues analysts encounter during the dissemination phase of report creation. These may seem basic, but it’s essential to ensure they’re solidly in place. Download now to explore these insights or read along!
Translating Threat Intelligence to Actionable Report 🔗︎
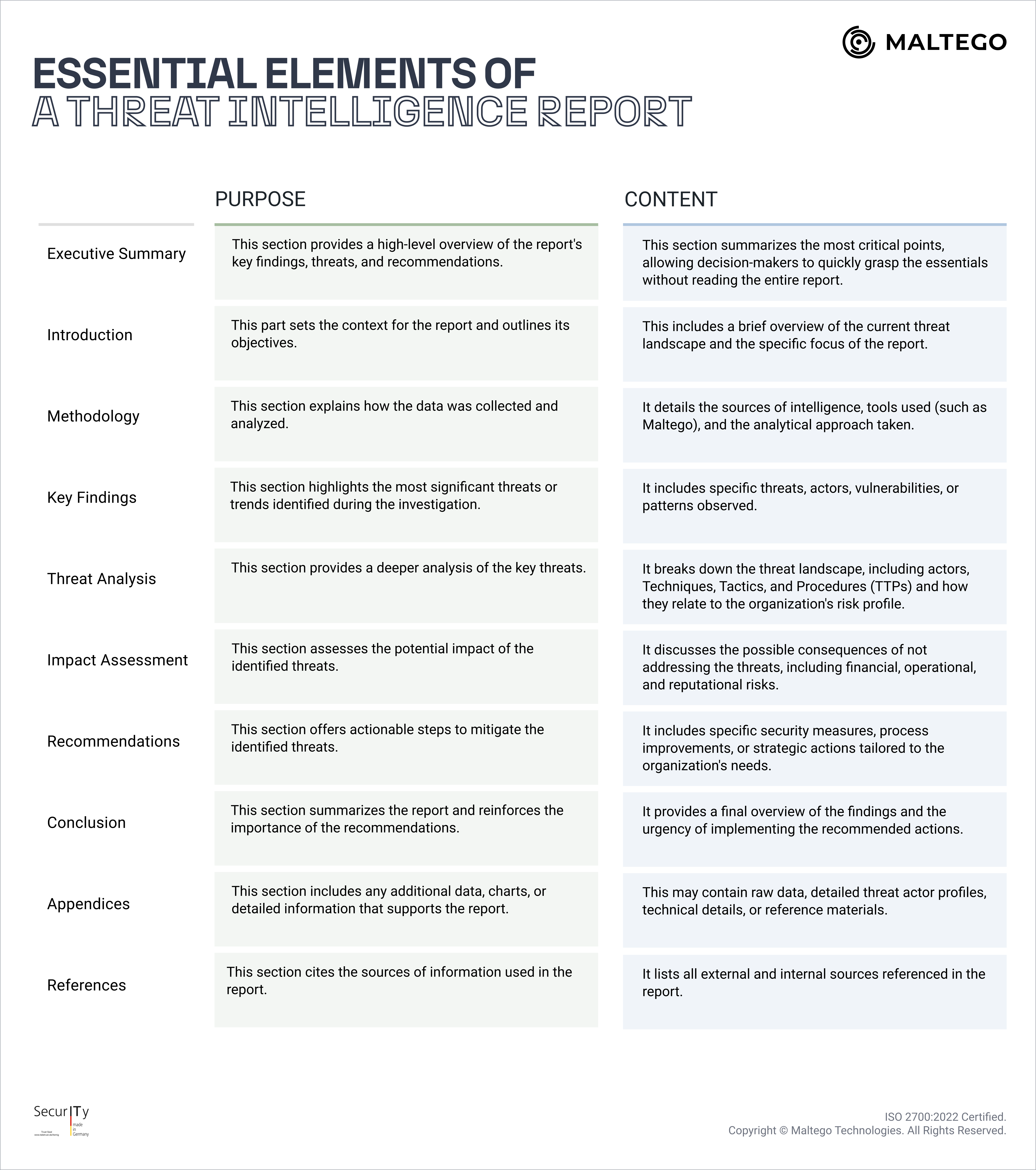
For a threat intelligence report to be truly effective, it must be structured to communicate the necessary information while guiding decision-makers toward actionable steps. Discover the critical elements that should be present in every threat intelligence report:
Essential Elements of a Threat Intelligence Report 🔗︎
These components form the backbone of a threat intelligence report. When structured effectively, they ensure that the report not only informs but also drives strategic action. Now that we’ve covered what must be included in the reports, let’s dive into the most important part of a threat intelligence report: how to operationalize it.
NOTE Depending on the type of intelligence you are writing about, additional components may need to be included. For instance, a threat actor profile should encompass identifiers, motivations, capabilities, and TTPs (Tactics, Techniques, and Procedures). For further guidance, refer to MITRE’s CTI Blueprints project for various examples of threat intelligence reports.
Download the Whitepaper to Get Hands-On Insights 🔗︎
The true value of a threat intelligence report isn’t just in the data it provides, but in how that data is interpreted and used to drive action. For the insights to translate into meaningful security improvements, analysts must include actionable recommendations—ranging from immediate and long-term actions to security controls and process changes—so the gathered intelligence can be fully operationalized.
Download our white paper to uncover solutions for overcoming key challenges in report creation. We’ve included the entire template of a threat intelligence report from an access broker investigation to clearly demonstrate how to translate threat intelligence into actionable steps!
Download the resource
Stay connected with us on X and LinkedIn, and subscribe to our email newsletter to stay updated with the latest news and developments.
Enjoy exploring the resource!
About the Author 🔗︎
Mario Rojas
Mario Rojas is a former Cyber Security and Threat Intelligence Subject Matter Expert at Maltego with more than 14 years of experience in the cybersecurity field. His expertise in open-source intelligence (OSINT) allows him to effectively map and visualize complex relationships and connections between entities, from IP addresses and domain names to social media profiles and dark web forums.