Profiling requires conducting in-depth research on a threat actor ranging from the strategic, tactical, and operational levels. And multiple angles need to be covered. In this article, we delve into the intricate process of profiling the threat actor known as “Scattered Spider,” illustrating various techniques for data collection and analysis using Maltego
Who is Scattered Spider? 🔗︎
Scattered Spider is a threat actor group that has been widely known because of their consistency and creativity. They can be identified by multiple names established by the different industry players who analyzed them. Those aliases include Tarfraud, UNC3944, Scattered Swine, Storm-0875, LUCR-3, Octo Tempest, Roasted Oktapus, and Muddle Libra.
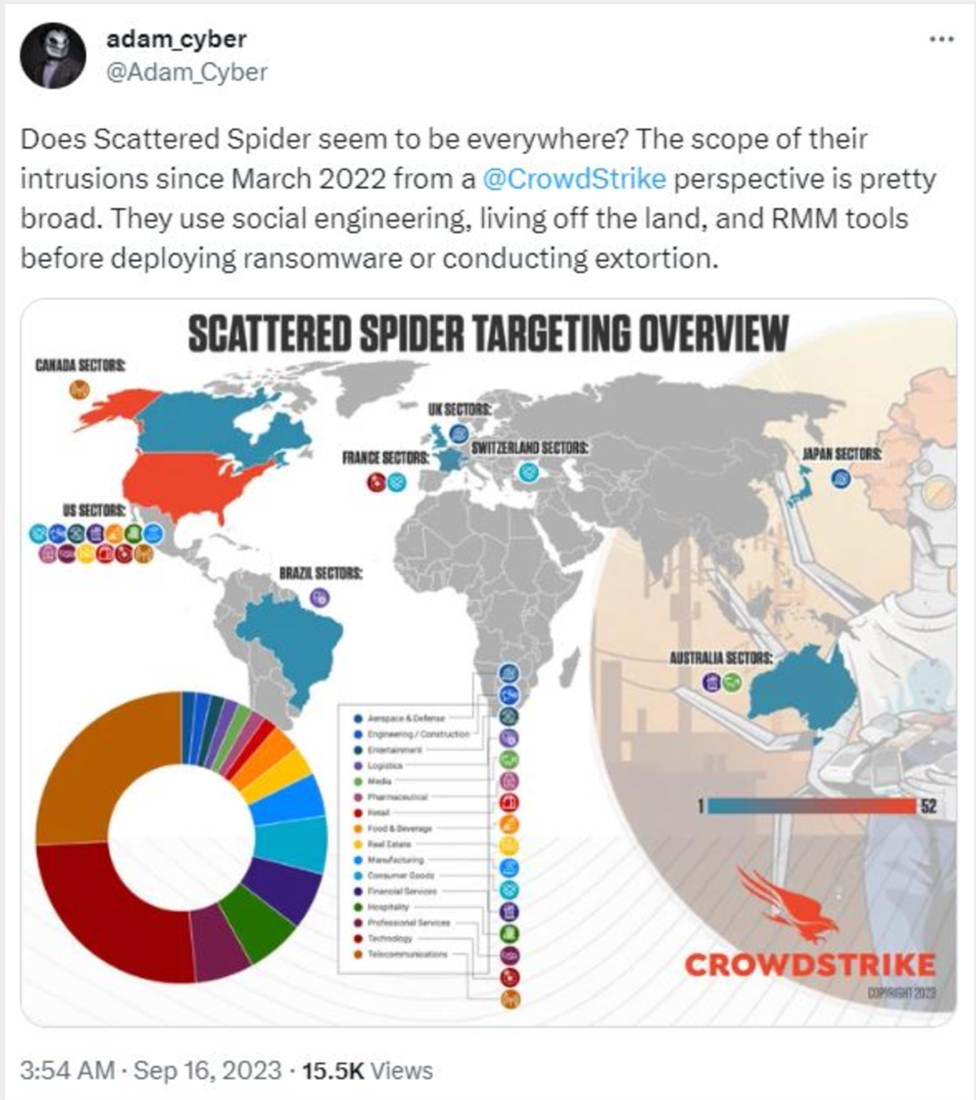
They have attacked hundreds of organizations worldwide since 2022, getting attention from the industry and other vendors such as CrowdStrike, Mandiant, Palo Alto Unit42, Trellix, SilentPush, and Group-IB. Their activities have even been featured on the CBS “60 Minutes” program.
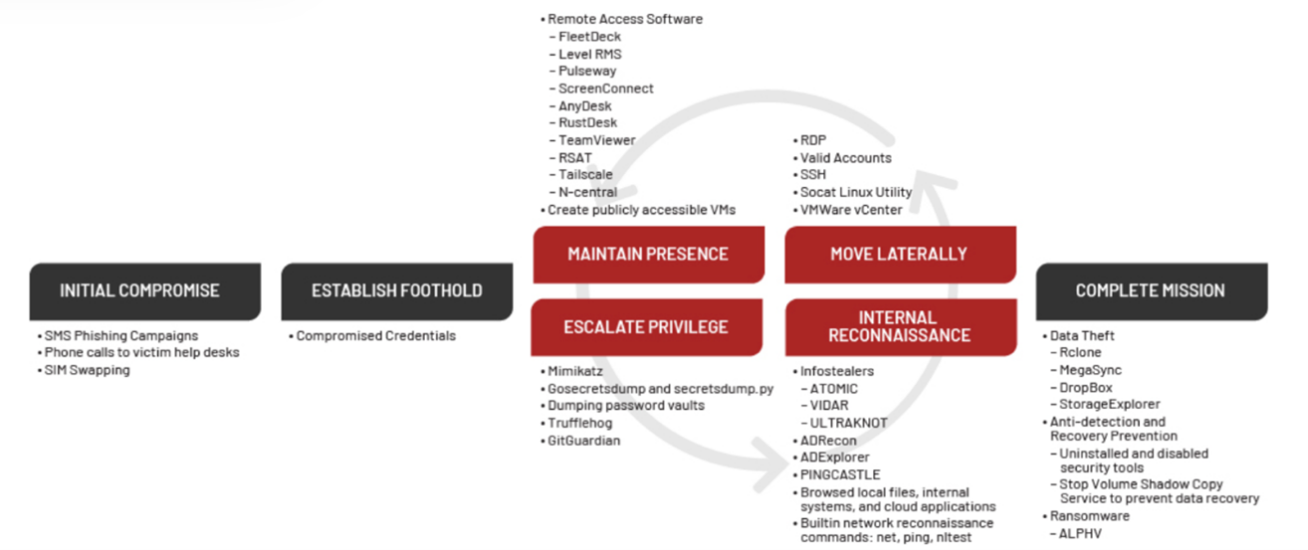
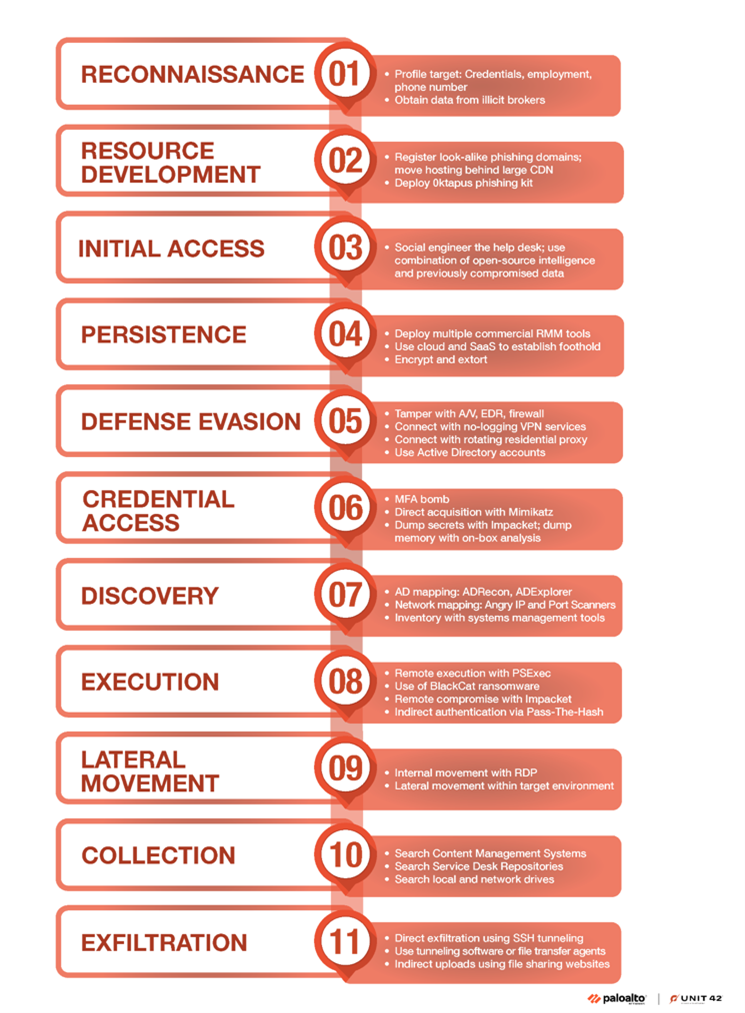
Scattered Spider employs a variety of social engineering techniques, such as SMS phishing and impersonation in help desk calls. They also abuse compromised credentials to establish a foothold in their victims. This foothold is preserved and escalated through the use of living off the land (LOTL) techniques and legitimate remote access software. Additionally, they have a special predilection for abusing privileged cloud environment resources.
Three Popular Cyber Attacks Orchestrated by Scattered Spider 🔗︎
The Scattered Spider group has conducted at least 3 remarkable campaigns so far:
- Oktapus / March-July 2022: This campaign targeted employees of U.S.-based companies that use services from IAM leader Okta. The attackers created over a hundred unique domains that mimic these organizations, incorporating keywords such as “sso,” “vpn,” “okta,” “mfa,” and “help.”
- C0027 / June-December 2022: This campaign focused on targeting mobile carriers, aiming to facilitate SIM-swapping attacks against victims.
- Mid-2022-January 2023: This period saw the group targeting large outsourcing firms that serve high-value cryptocurrency institutions and individuals.
It’s important to note that in mid-2023, as reported by Unit42 from Palo Alto Networks, Scattered Spider began shifting their tactics to deploy ransomware in victim environments. This marks a significant change in the group’s monetization strategies, indicating an evolution in their behavioral patterns.
Scattered spider has effectively targeted victims using breached or stolen data, and they repeatedly return to the well to update their stolen dataset. Even after initial incident responses, they use this data to re-target previous victims. This group has consistently demonstrated a profound understanding of modern incident response processes, enabling them to persistently advance toward their goals and maintain access to victim networks, despite efforts by responders to remove them.
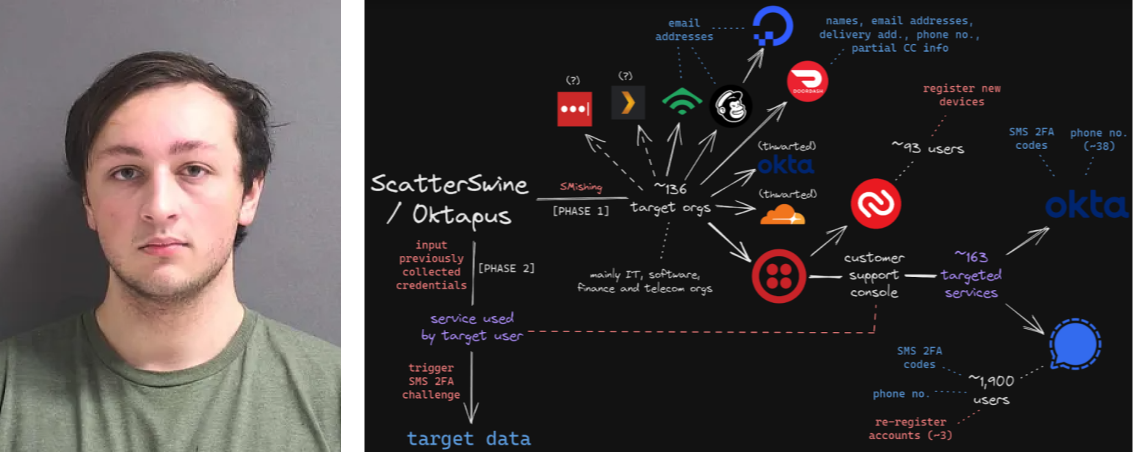
Early this year, the industry was surprised by the arrest of an individual named Michael Urban who uses the aliases “Sosa” and “King Bob” on alleged charges of SIM-swapping activities over different victims. As the cybercrime journalist, Brian Krebs, states, he was a top member of the broader cybercriminal community online known as “The Com,” wherein hackers boast loudly about high-profile exploits and hacks that almost invariably begin with social engineering — tricking people over the phone, email or SMS into giving away credentials that allow remote access to corporate internal networks. Sosa was also active in a particularly destructive group of accomplished criminal SIM swappers known as “Star Fraud.” Cyberscoop’s AJ Vicens reported last year that individuals within Star Fraud were likely involved in the high-profile Caesars Entertainment and MGM Resorts extortion attacks.
Based on the reports and similar TTPs he employed, it is reasonable to assume that Mr. Urban might have close ties to the activities of the Scattered Spider group.
Download the White Paper for Expert Tips! 🔗︎
In our whitepaper, we outline detailed techniques for data collection and analysis, specifying what and where to gather crucial Intelligence. We also present several effective methods for collecting threat intelligence using OSINT, threat intelligence communities, and private intelligence providers. The information is presented in a step-by-step format, making full use of Maltego’s seamless data integrations. The whitepaper enables readers to:
- Identify relevant cyber threat intelligence data and sources.
- Understand effective methods for collecting treat Intelligence from these sources.
- Analyze the collected intelligence, enhance its integration, and enrich it with additional data sources.
Download the whitepaper to gather and analyze real-time intelligence with Maltego!
Download the resource
Don’t forget to follow us on Twitter and LinkedIn and sign up for our email newsletter, so you don’t miss out on updates and news!
Happy investigating!
About the Authors 🔗︎
Carlos Fragoso
Carlos is the Principal Subject Matter Expert and Lead Instructor at Maltego with over 20 years of professional experience in information security: Incident response, digital forensics, threat intelligence, and threat hunting. A curious and passionate investigator working with big companies and LEAs to tackle cybercrime around the world (Europe, Middle East, LATAM) SANS Institute Instructor.
Acknowledgements:
We were excited to undertake this research to support our users and honor the InfoSec community, which tirelessly works to prevent cybercrimes. We recognize that many CTI teams face numerous requests and lack the time to manage all their data sources effectively. Our goal was to inspire them by demonstrating how Maltego can streamline this process and enhance various data integrations within one platform. Scattered Spider is just one of many threats, and we will continue to stand by your side to tackle them together.
Exciting developments are on the horizon—stay tuned for more updates!
Mathieu Gaucheler
Mathieu is a Subject Matter Expert at Maltego. His responsibilities include research-driven content development for blog posts, webinars, and talks. He started working in cybersecurity in Barcelona, focusing on malware analysis and sandbox development. He has previously presented his research at BotConf and RSA APJ.
Acknowledgements:
We trust that this article will not only provide insights into tracking threat actors across diverse datasets using Maltego, but also offer guidance on leveraging the fusion of these datasets to advance your investigations. By delving into the intricacies of combining various data sources, we aim to equip you with the knowledge needed to extend the scope and depth of your investigative efforts. It has been a privilege to play a role in this journey, and we remain committed to continually simplifying the process of analyzing threat intelligence.