Many of us recall the days when we innocently created fake profiles on social media during our adolescence or used cheat codes in games like The Sims to build lavish mansions. Most would agree that these actions, while bending the rules, were benign and are a far cry from the more severe product and platform abuses.
Where Pushing Boundaries Ends and Product Abuse Begins 🔗︎
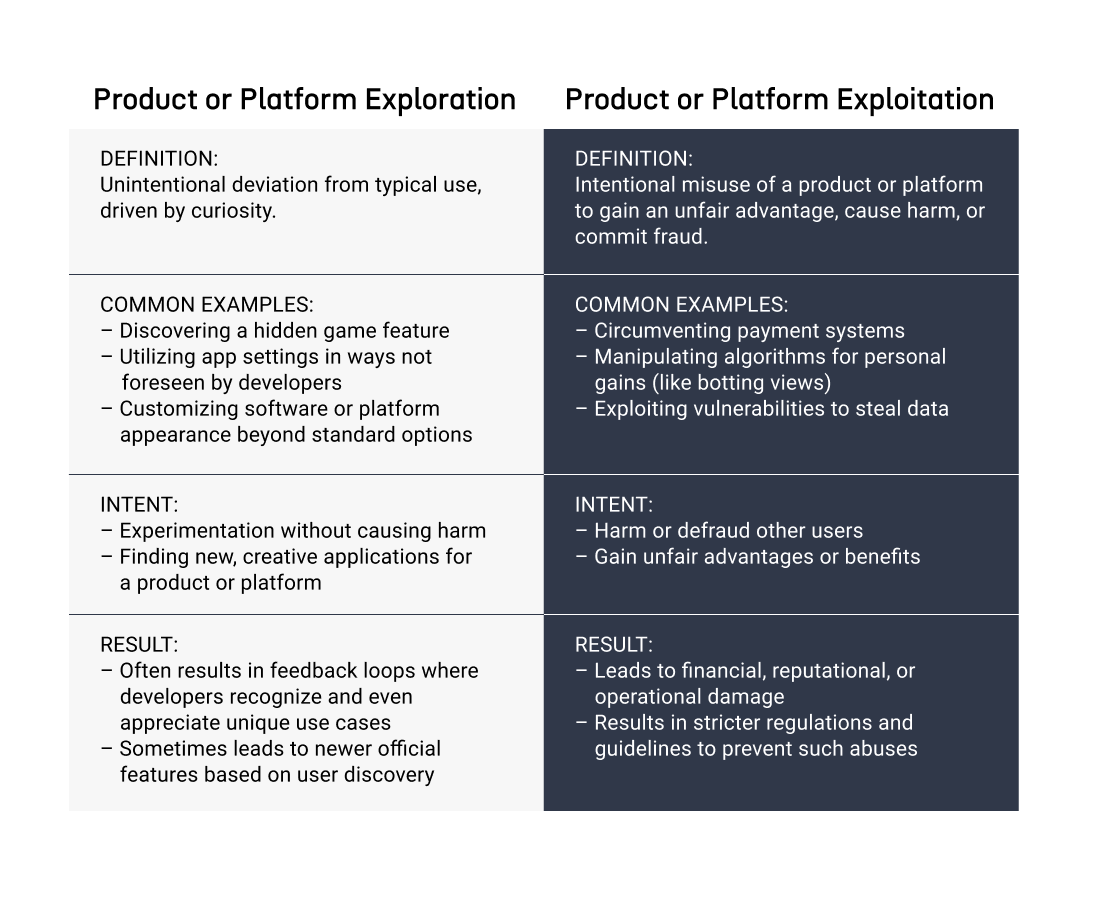
While it’s easy to jump to the conclusion that product or platform abuse is synonymous with malicious intent, this isn’t always the case. Many instances of what we label as “abuse” might simply be curious users discovering novel ways to utilize a platform or product. They stumble upon new, unintended ways to use a product or platform, driven by curiosity rather than malice.
This benign exploration shouldn’t overshadow a significant concern: for every user pushing boundaries out of innocent curiosity, there are malicious actors diligently searching for loopholes to exploit for their gain.
These graver offenses include malicious activities such as scams, bullying, and doxing, and their repercussions can be severe, leading to reputational damage, financial losses, or breaches in operational security.
Reflecting on the past decade or so, it’s commendable how far products and platforms have evolved in their fight against abuse. They’ve tightened security, refined user guidelines, and enhanced monitoring mechanisms. Yet, given the uptick in malicious abuse, platforms must redouble their preventive efforts.
If you want to find out more about examples of real-life product and platform abuse, the full version of this blog article covers six case studies of abuse experienced by leading global companies and offers strategies to protect your brand. Download your copy now!
The Scale of Product and Platform Abuse in Numbers 🔗︎
The extent of product and platform abuse is challenging to measure accurately, primarily because each platform maintains its proprietary data on misuse and every country keeps its distinct records of online harassment.
To offer some perspective on the scale of this issue:
- A 2021 study by Pew Research Center revealed that a staggering 41% of Americans have experienced online harassment at some point.
- Between 2017 and 2018, England and Wales reported 1,605 online hate crimes. This number, while seemingly specific, only scratches the surface of global incidents.
- While the same study estimates that only about 1% of online content is abusive, it’s crucial to understand the vastness of the digital sphere. Even 1% translates to a monumental amount of abusive content when considering the billions of digital interactions taking place daily.
- Interestingly, abuse tends to concentrate more on niche platforms. For instance, platforms like 4Chan, which cater to a more specific user base, are estimated to contain as much as 8% abusive material.
- Reflecting on German statistics, the country recorded a significant 146,363 instances of reported cyber crimes in 2021. Worryingly, only 29.3% of these cases were solved.
The data highlights a grim truth: abuse in the digital realm is pervasive and often goes unchecked.
Tangible and Intangible Consequences for Organizations and Users 🔗︎
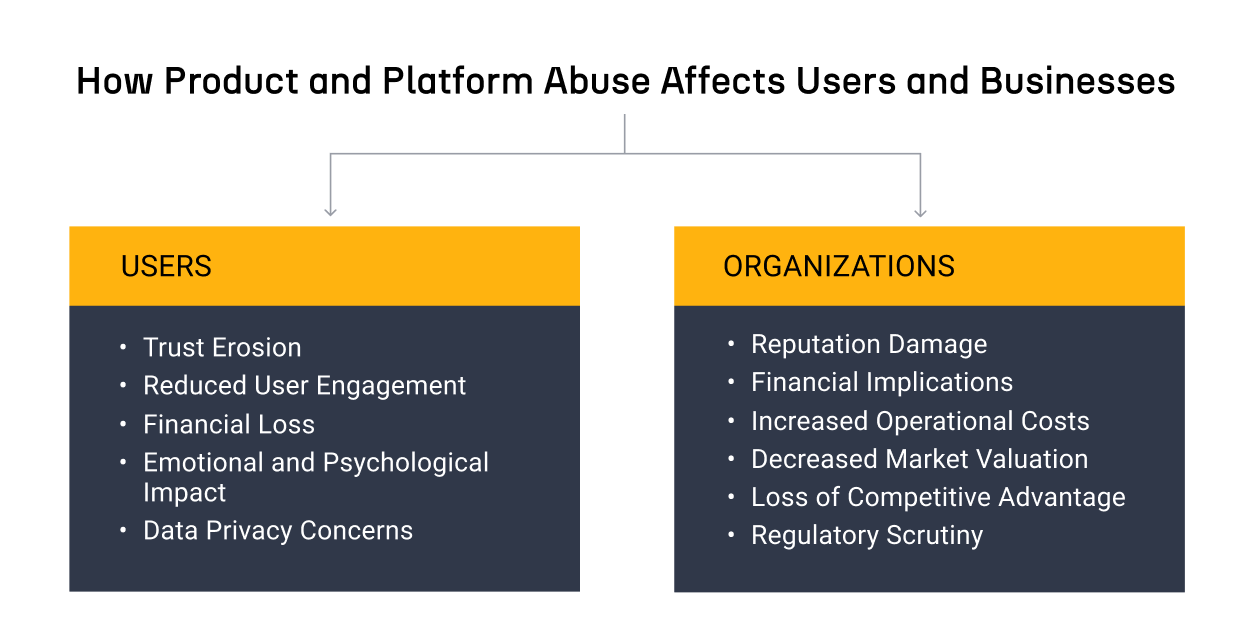
From a business standpoint, the effects of product and platform abuse are multi-faceted, affecting organizations and users.
For Users: 🔗︎
For Organizations: 🔗︎
Insights from Real-Life Product Abuses across Industries 🔗︎
While we often focus on the theoretical aspects of product and platform abuse, understanding the real-world implications offers businesses not only actionable insights but also promotes risk mitigation and can help safeguard their reputation.
To highlight the gravity of product abuse, we’ve created a whitepaper with six case studies from prominent global companies that have faced abuse. Each case provides insights and lessons for businesses looking to strengthen their defenses against such threats.
Download This PDF to Gain Insight into 🔗︎
- Direct experiences of renowned companies grappling with product and platform abuse
- Effective strategies to neutralize and prevent these challenges
- Key areas for Trust and Safety teams to concentrate on to maximize their efforts
Download the resource
If you’re keen on exploring the hands-on aspects of Trust and Safety operations, you may want to delve into how mapping tools enhance the efficiency and effectiveness of these dedicated teams on a daily basis.
Don’t forget to follow us on Twitter, LinkedIn, and Mastodon, and sign up to our email newsletter to stay updated on the latest tutorials, use cases, and webinars!
Happy investigating!
About the Author 🔗︎
Jules Brahms
Jules Brahms is a Subject Matter Expert at Maltego, where she supports the trust and safety needs of brands, companies, and platforms, drawing on her experience as a trust and safety professional with a background in incident response, product abuse, and misinformation prevention. In her role, she develops workflows for trust and safety practitioners and conducts training with teams to build capacity in risk assessments, the handling of misinformation and electoral manipulation, and person of interest investigations. Previously, Jules worked as a Subject Matter Expert for online radicalization and misinformation at trust and safety provider ActiveFence, which delivers trust and safety solutions to leading online platforms.