In the previous post, we derived DNS names from a given domain. That returned hostnames which are, or have historically been, part of the domain’s infrastructure.
Continuing Level 1 Network Footprint with Maltego 🔗︎
In this post we explore the next step in mapping the Level 1 network footprint - deriving the IP addresses of the hostnames and the netblock these IP addresses belong to.
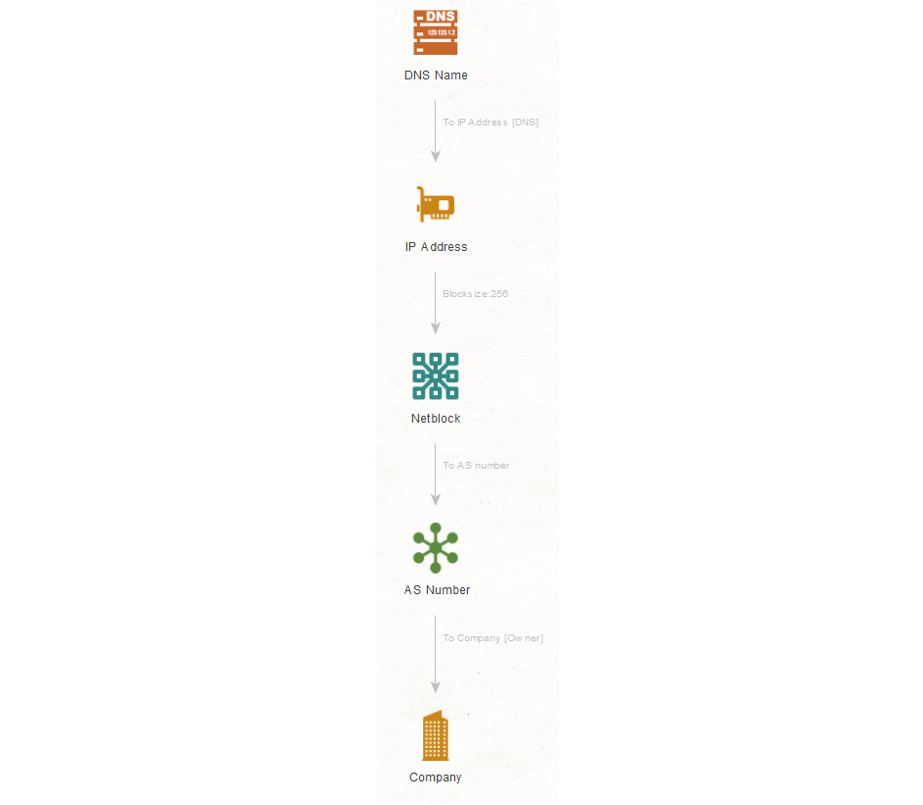
At each step in this sequence, we run a Transform on the output Entities of the previous Transform.
Step 1: Pivoting from DNS Names 🔗︎
We start with the DNS Names from the previous post and run the Transform To IP Address [DNS] to obtain IP addresses. This Transform resolves the input Entity using DNS to IP addresses.
Step 2: Deriving The Netblocks from IP Addresses 🔗︎
Next, we derive the netblocks the IP addresses are part of by running the To Netblock [Using natural boundaries] Transform. This Transform by default divides the IP address space into blocks of 256 IP addresses and returns the block where the given IP address fits into. The block size can be configured in the Transform input (little spanner icon next to the Transform’s name in the Transform menu).
How is Netblock Information Obtained 🔗︎
Netblock information can also be obtained from the routing updates published by the Border Gateway Protocol (BGP) on the Internet backbone. The To Netblock [Using routing info] Transform uses this information to assign a netblock to a given IP address.
As with the natural boundaries, we must make a few assumptions regarding the size and validity of the netblocks. The size and validity of the netblock of an IP address depends on the BGP routing view used by the Transform. Therefore, we may get a smaller (or more precise) or larger (less precise) netblock with this Transform. Moreover, the netblock size may not reflect all the recent changes made to it as there is a delay in generating the routing views from BGP routing updates.
Step 3: Return the AS Number Owning the Netblocks 🔗︎
We now pivot on the returned netblocks to derive the Autonomous System (AS) that own them. For this we use the To AS number Transform. This Transform returns the owner of a given netblock by querying the Regional Internet Registry (RIR) databases.
Step 4: Finding Out the Owner of the AS Numbers 🔗︎
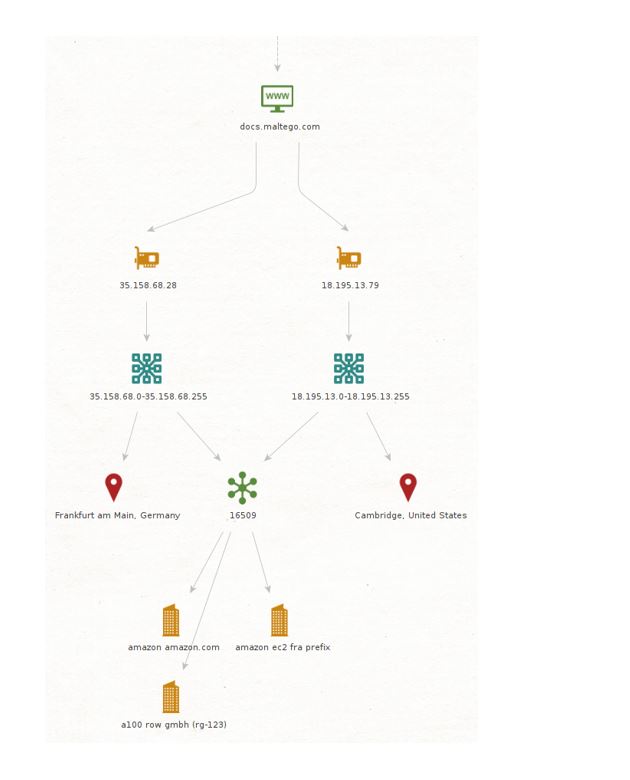
Finally, we derive the owner of the returned AS numbers by running the To Company [Owner] Transform. This Transform extracts the owner information of a given AS from the RIR databases. Running the above Transforms on the docs.maltego.com DNS Name Entity shows that docs.maltego.com is hosted on Amazon AWS:
Uncovering Internet Infrastructure By Conducting Level 1 Network Footprint 🔗︎
In this post, we have seen how to derive IP addresses, netblocks, AS numbers, and the AS owners. This, together with deriving DNS hostnames from a domain name, comprises a Level 1 network footprint. It shows us the Internet infrastructure used by services that are provided under a domain name. As companies usually offer their services under their company domain, this footprint maps the infrastructure the company uses for providing the services/products it offers.
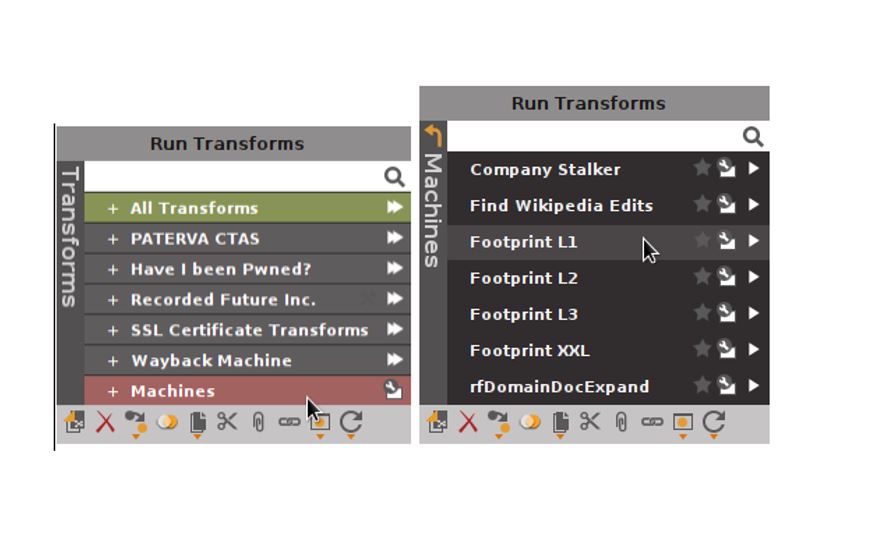
If you made it this far, congratulations! L1 foot-printing is common in IT security and running the Transforms introduced in Part 1 and this blog post for new domains is repetitive and tedious. Therefore, Maltego comes with the L1 footprint machine.
Automate Level 1 Network Footprint with Maltego Machines 🔗︎
Machines are like macros that execute a fixed set of Transforms. Learn more about Machines and how to create them this blog post.
You can have all the above Transforms run in the same order by running the L1 footprint machine. To run a machine, click on the Machines > Footprint L1 with your starting Domain Entity selected, and then wait for the magic to complete.
To stay up to date with other cool use cases, product updates and Maltego events, follow us on Twitter or LinkedIn or subscribe to our email newsletter. If you have questions, requests, or use cases you’d like to share, we would love to hear from you on Twitter!


 4.5 rating
4.5 rating